Cryptographic Keys 101: What They Are & How They Secure Data - Hashed Out by The SSL Store™
Por um escritor misterioso
Last updated 03 março 2025

Cryptographic keys, in combination with an encryption algorithm, disguise data (encryption) so only a special key can access it (decryption).
The SSL Store: What Is a Hash Function in Cryptography? A
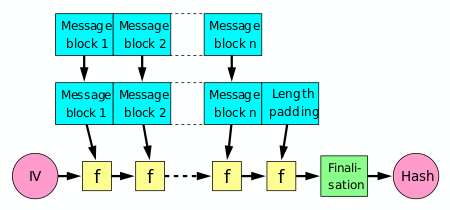
Cryptographic hash function - Wikipedia

Trusted Platform Module - Wikipedia

PII Encryption Protect Your Customer's Privacy

The SSL Store: ACME Protocol: What it is and how it works 05/31

HashedOut: Open standards for three #quantumcryptography
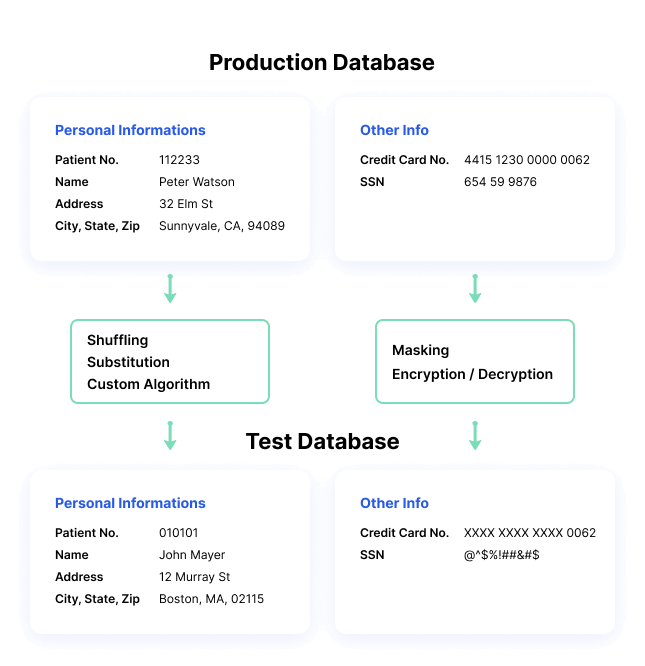
What is Data Masking?, Techniques & Best Practices
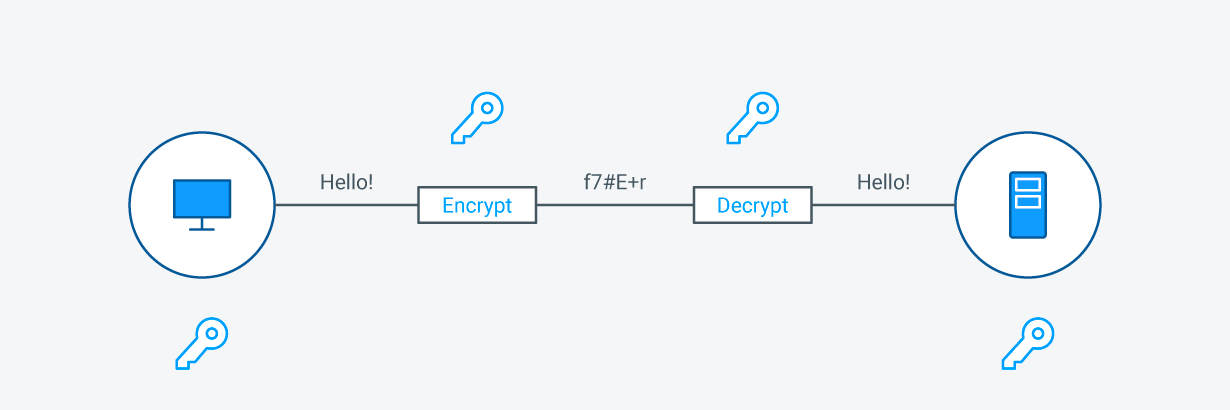
What is SSL Cryptography?
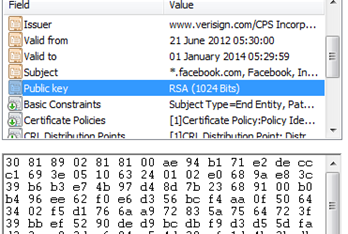
Cryptography 101 with SSL
Recomendado para você
-
 LURLIN Mixed Set of 30 Large Skeleton Keys with Antique Style Bronze Brass Skeleton Castle Dungeon Pirate Keys for Birthday Party Favors, Mini03 março 2025
LURLIN Mixed Set of 30 Large Skeleton Keys with Antique Style Bronze Brass Skeleton Castle Dungeon Pirate Keys for Birthday Party Favors, Mini03 março 2025 -
 Clever Organisation for Better Living – Orbitkey03 março 2025
Clever Organisation for Better Living – Orbitkey03 março 2025 -
 Roof Rack Keys Cut -FREE POST IN Aust03 março 2025
Roof Rack Keys Cut -FREE POST IN Aust03 março 2025 -
 Rad Replacement Keys03 março 2025
Rad Replacement Keys03 março 2025 -
 What to Do When You Lose Your Key03 março 2025
What to Do When You Lose Your Key03 março 2025 -
 How to Recycle Keys or Put Them to Good Use03 março 2025
How to Recycle Keys or Put Them to Good Use03 março 2025 -
 The Secret to Finding Lost Keys Revealed – Pebblebee03 março 2025
The Secret to Finding Lost Keys Revealed – Pebblebee03 março 2025 -
:max_bytes(150000):strip_icc()/__opt__aboutcom__coeus__resources__content_migration__mnn__images__2009__12__main_chanie_keys-06c395c828514db7aac45a3dcf64b0eb.jpg) What Can I Do With All My Old, Useless Keys?03 março 2025
What Can I Do With All My Old, Useless Keys?03 março 2025 -
 Do Not Copy Keys - What it all means - Wynns Locksmiths03 março 2025
Do Not Copy Keys - What it all means - Wynns Locksmiths03 março 2025 -
 Lowe's Nickel Plated #66 Kwikset Brass House/Entry Key Blank03 março 2025
Lowe's Nickel Plated #66 Kwikset Brass House/Entry Key Blank03 março 2025
você pode gostar
-
 Glenn Leroi – SCP-079 Song (alternate extended version) Lyrics03 março 2025
Glenn Leroi – SCP-079 Song (alternate extended version) Lyrics03 março 2025 -
 Orange Rainbow Friends Svg, Orange Rainbow Svg, Rainbow Frie03 março 2025
Orange Rainbow Friends Svg, Orange Rainbow Svg, Rainbow Frie03 março 2025 -
American Clinical Experience03 março 2025
-
 Images Green Rainbow Friends Coloring Pages - Free Printable Coloring Pages03 março 2025
Images Green Rainbow Friends Coloring Pages - Free Printable Coloring Pages03 março 2025 -
Blanco Digital03 março 2025
-
 The Legend Of Zelda: Breath Of The Wild Sequel Delayed To Spring03 março 2025
The Legend Of Zelda: Breath Of The Wild Sequel Delayed To Spring03 março 2025 -
 Fairy Tail Gekitotsu! Kardia Daiseidou, Fairy Tail Wiki03 março 2025
Fairy Tail Gekitotsu! Kardia Daiseidou, Fairy Tail Wiki03 março 2025 -
 Explore the Best Getbackers Art03 março 2025
Explore the Best Getbackers Art03 março 2025 -
 Waifu Makima Power Hentai Ecchi Chainsaw Man Anime Kiss-Cut Sticker Vinyl Decal03 março 2025
Waifu Makima Power Hentai Ecchi Chainsaw Man Anime Kiss-Cut Sticker Vinyl Decal03 março 2025 -
 Free STL file Torino FC - Logo 📛・3D printable model to download・Cults03 março 2025
Free STL file Torino FC - Logo 📛・3D printable model to download・Cults03 março 2025

