PDF] Figure 1: Architecture of XSS attack Injection of code into
Por um escritor misterioso
Last updated 23 janeiro 2025
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://d3i71xaburhd42.cloudfront.net/c976c25cbfcac95b7f9ca9b5783a731a75426605/1-Figure1-1.png)
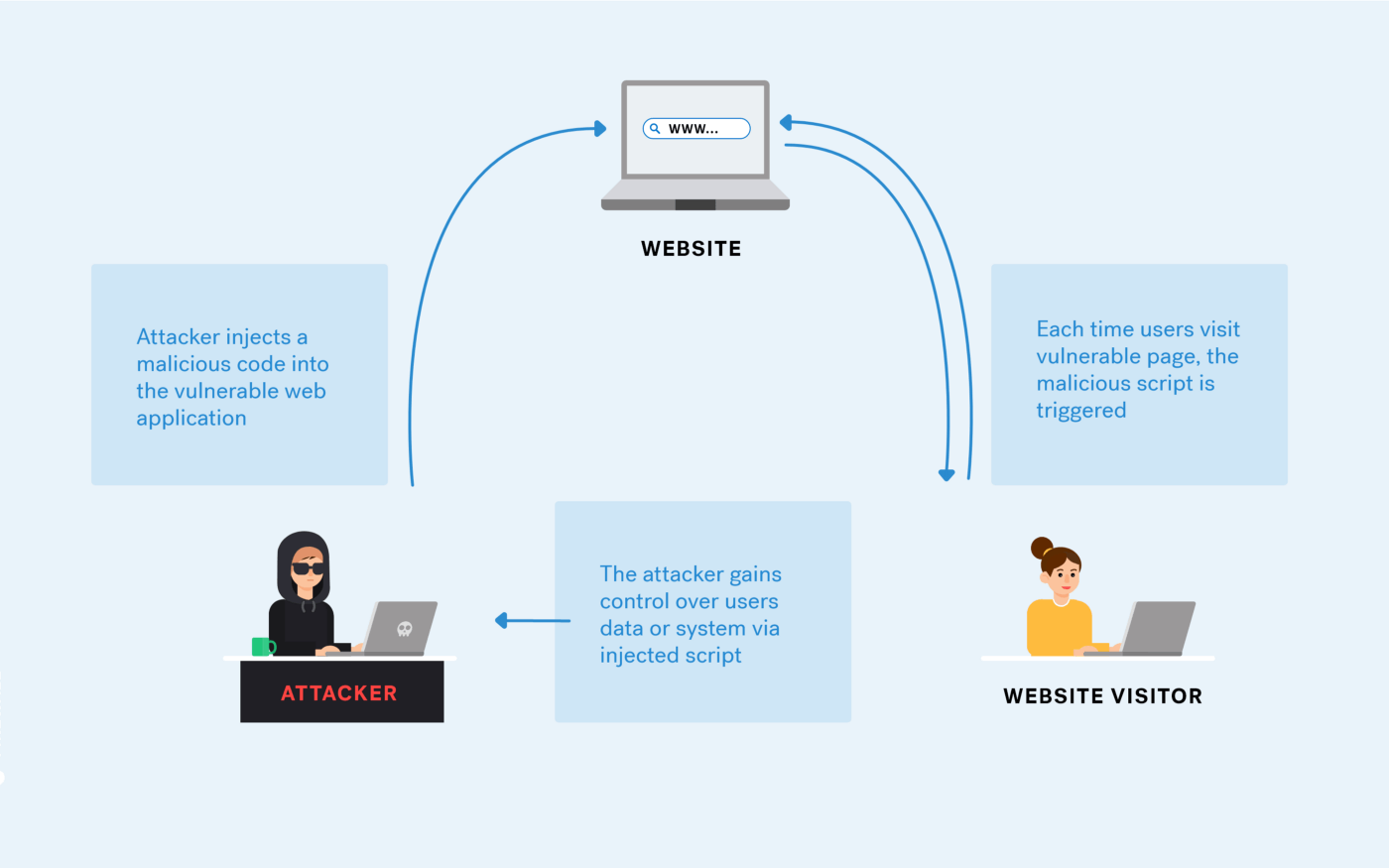
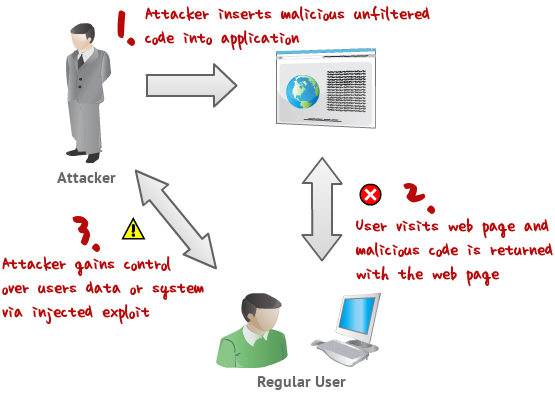
This work aims at developing a solution in web applications undergo rigorous testing by being a target to the engine and consequently finding flaws embedded within them. 549 Published By: Blue Eyes Intelligence Engineering & Sciences Publication Retrieval Number: F2318037619/19©BEIESP Abstract: Web applications actively replace native applications due to their flexible nature. They can be easily deployed and scaled, which require constant interaction with the user machine for software updates. Widespread use of cloud computing [10] has resulted in favoring web applications for easy deployment and scalability. Today the movement of software applications to the web has resulted to web application vulnerabilities [1]. Instead of targeting multiple operating systems or platforms, attackers can focus on exploiting web applications for compromising sensitive information. Web browsers act as the interface between the user and the web and are crucial for user security. The client-side attacks can result in the compromise of credentials and identity theft. In this paper, totally three models are developed namely Injection of code into un-sanitized parameters, Browser exploitation techniques and Manipulation of application registries which serve as the basis for exploiting and subsequently preventing cross-site scripting vulnerabilities [3]. By using these models as a foundation, the attacks are minimized in a large scale. In this work the results shows that, for the random sample of attack vectors 4, 2, 9, the vulnerability score is 0, which is considered to be minimum and forth random sample of attack vectors 2, 5, 7 the vulnerability score is 89.12 which is considered to be maximum. This work aims at developing a solution in web applications undergo rigorous testing by being a target to the engine and consequently finding flaws embedded within them.
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://file.techscience.com/files/cmc/2023/TSP_CMC-76-3/TSP_CMC_40121/TSP_CMC_40121/Images/CMC_40121-fig-5.png/mobile_webp)
CMC, Free Full-Text
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://0.academia-photos.com/attachment_thumbnails/6784475/mini_magick20190427-11529-voss8p.png?1556367780)
PDF) Automatic creation of SQL injection and cross-site scripting attacks
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.getastra.com/blog/wp-content/uploads/2017/04/1ff44ec3-e5bc-40b6-a633-d8c70b8a5f2a.gif)
Cross-site Scripting (XSS) Attack: All You Need to Know - Astra Security Blog
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://miro.medium.com/v2/resize:fit:712/1*Gr8Sw8nEpV8SKMz8rBRL_A.jpeg)
Remote MS Office template injection, by Tho Le
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://image.slidesharecdn.com/ijcatr03101001-141111002535-conversion-gate01/85/study-of-crosssite-scripting-attacks-and-their-countermeasures-1-320.jpg?cb=1669878105)
Study of Cross-Site Scripting Attacks and Their Countermeasures
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/m685/springer-static/image/art%3A10.1186%2Fs13174-019-0115-x/MediaObjects/13174_2019_115_Fig1_HTML.png)
Detecting web attacks with end-to-end deep learning, Journal of Internet Services and Applications
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://html.scirp.org/file/2-9702501x3.png?20220808173255347)
Cross-Site Scripting Attacks and Defensive Techniques: A Comprehensive Survey*
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/full/springer-static/image/art%3A10.1038%2Fs41598-023-46640-9/MediaObjects/41598_2023_46640_Fig1_HTML.png)
A survey on performance evaluation of artificial intelligence algorithms for improving IoT security systems
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://secops.group/wp-content/uploads/2023/08/image14.png)
A Deep Dive into Server-Side JavaScript Injection (SSJI) Vulnerabilities • The SecOps Group
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://image.slidesharecdn.com/xss-230809140851-e76e5097/85/xsspdf-5-320.jpg?cb=1691590450)
XSS.pdf
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/m685/springer-static/image/art%3A10.1186%2Fs40537-022-00678-0/MediaObjects/40537_2022_678_Fig3_HTML.png)
Detection and prevention of SQLI attacks and developing compressive framework using machine learning and hybrid techniques, Journal of Big Data
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://d3i71xaburhd42.cloudfront.net/c976c25cbfcac95b7f9ca9b5783a731a75426605/5-Table2-1.png)
PDF] Figure 1: Architecture of XSS attack Injection of code into un-sanitized parameters, Browser exploitation techniques and Manipulation of application registries which serve as the basis for exploiting and subsequently preventing cross-site
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://www.mdpi.com/jcp/jcp-01-00018/article_deploy/html/images/jcp-01-00018-g002.png)
JCP, Free Full-Text
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/m685/springer-static/image/art%3A10.1186%2Fs13174-019-0115-x/MediaObjects/13174_2019_115_Fig7_HTML.png)
Detecting web attacks with end-to-end deep learning, Journal of Internet Services and Applications
![PDF] Figure 1: Architecture of XSS attack Injection of code into](https://media.springernature.com/lw685/springer-static/image/art%3A10.1007%2Fs10462-023-10433-3/MediaObjects/10462_2023_10433_Fig12_HTML.png)
Detection of cross-site scripting (XSS) attacks using machine learning techniques: a review
Recomendado para você
-
 A Pentester's Guide to Cross-Site Scripting (XSS)23 janeiro 2025
A Pentester's Guide to Cross-Site Scripting (XSS)23 janeiro 2025 -
What is cross-site scripting (XSS) and how to prevent it?23 janeiro 2025
-
 SQL injection and cross-site scripting: The differences and attack23 janeiro 2025
SQL injection and cross-site scripting: The differences and attack23 janeiro 2025 -
 XSS Tutorial23 janeiro 2025
XSS Tutorial23 janeiro 2025 -
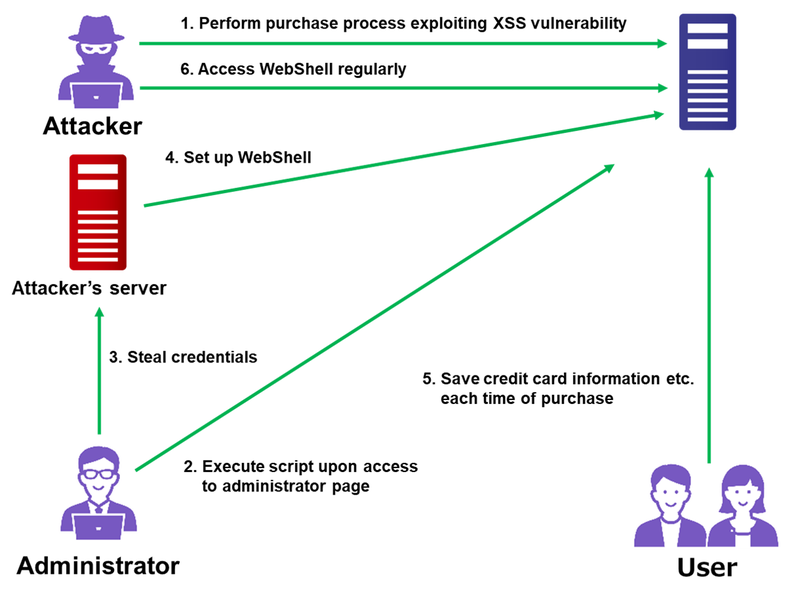 Attack Exploiting XSS Vulnerability in E-commerce Websites23 janeiro 2025
Attack Exploiting XSS Vulnerability in E-commerce Websites23 janeiro 2025 -
 SQL vs. XXS Injection Attacks Explained – I Help Women In Tech23 janeiro 2025
SQL vs. XXS Injection Attacks Explained – I Help Women In Tech23 janeiro 2025 -
![PDF] A threat pattern for the cross-site scripting (XSS) attack](https://d3i71xaburhd42.cloudfront.net/94255f6c397c3e4818a31959a464e97318a01608/5-Figure2-1.png) PDF] A threat pattern for the cross-site scripting (XSS) attack23 janeiro 2025
PDF] A threat pattern for the cross-site scripting (XSS) attack23 janeiro 2025 -
 SQL Injection attack using the XSS23 janeiro 2025
SQL Injection attack using the XSS23 janeiro 2025 -
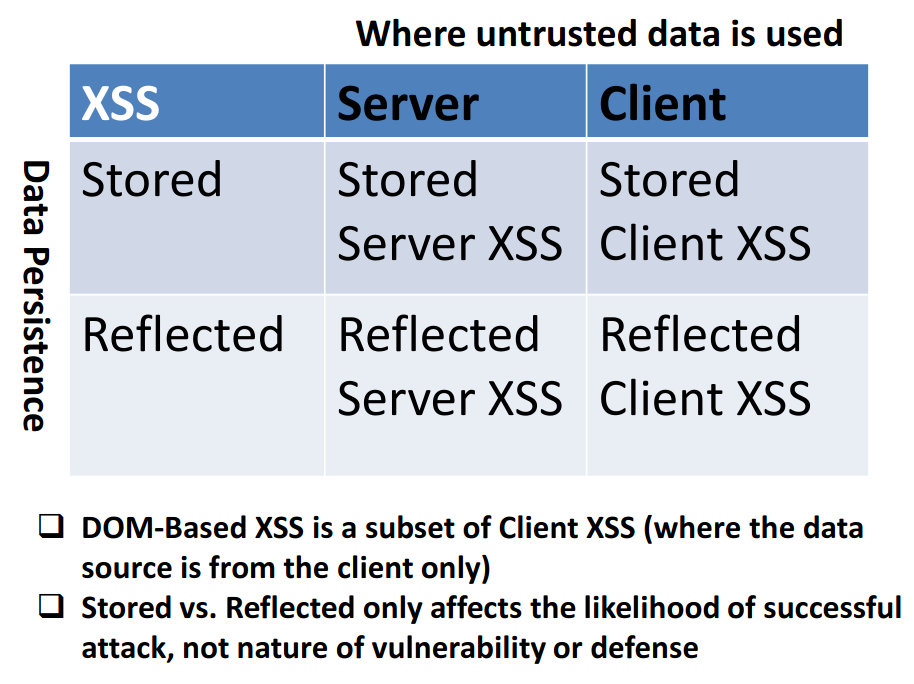 Types of XSS OWASP Foundation23 janeiro 2025
Types of XSS OWASP Foundation23 janeiro 2025 -
 Lab - XSS and CORS João Paulo Barraca23 janeiro 2025
Lab - XSS and CORS João Paulo Barraca23 janeiro 2025
você pode gostar
-
 UML use case diagrams with draw.io - draw.io23 janeiro 2025
UML use case diagrams with draw.io - draw.io23 janeiro 2025 -
 Yofukashi no Uta Official Fanbook (Call of the Night) - ISBN:978409851333823 janeiro 2025
Yofukashi no Uta Official Fanbook (Call of the Night) - ISBN:978409851333823 janeiro 2025 -
![RE5] Chris Dante Mod [Resident Evil 5] [Mods]](https://images.gamebanana.com/img/ss/mods/6128dad3e1c7f.jpg) RE5] Chris Dante Mod [Resident Evil 5] [Mods]23 janeiro 2025
RE5] Chris Dante Mod [Resident Evil 5] [Mods]23 janeiro 2025 -
 The Best Ping-Pong Tables23 janeiro 2025
The Best Ping-Pong Tables23 janeiro 2025 -
Fique dentro e desfrute de - Clube Desportivo 1º de Agosto23 janeiro 2025
-
Military Tower Defense Review – GameSkinny23 janeiro 2025
-
 Smileheart110 - Hobbyist, Digital Artist23 janeiro 2025
Smileheart110 - Hobbyist, Digital Artist23 janeiro 2025 -
Giveaway Bot [Update DO NOT USE]23 janeiro 2025
-
Ex 2022-10-05, PDF, Orçamento governamental23 janeiro 2025
-
 Not Too Late: A Brat-Style Honda CB500 Four23 janeiro 2025
Not Too Late: A Brat-Style Honda CB500 Four23 janeiro 2025


