Malware analysis Malicious activity
Por um escritor misterioso
Last updated 03 março 2025

Playbook for Malware outbreak

AlienVault - Open Threat Exchange

Malware analysis index.html Malicious activity
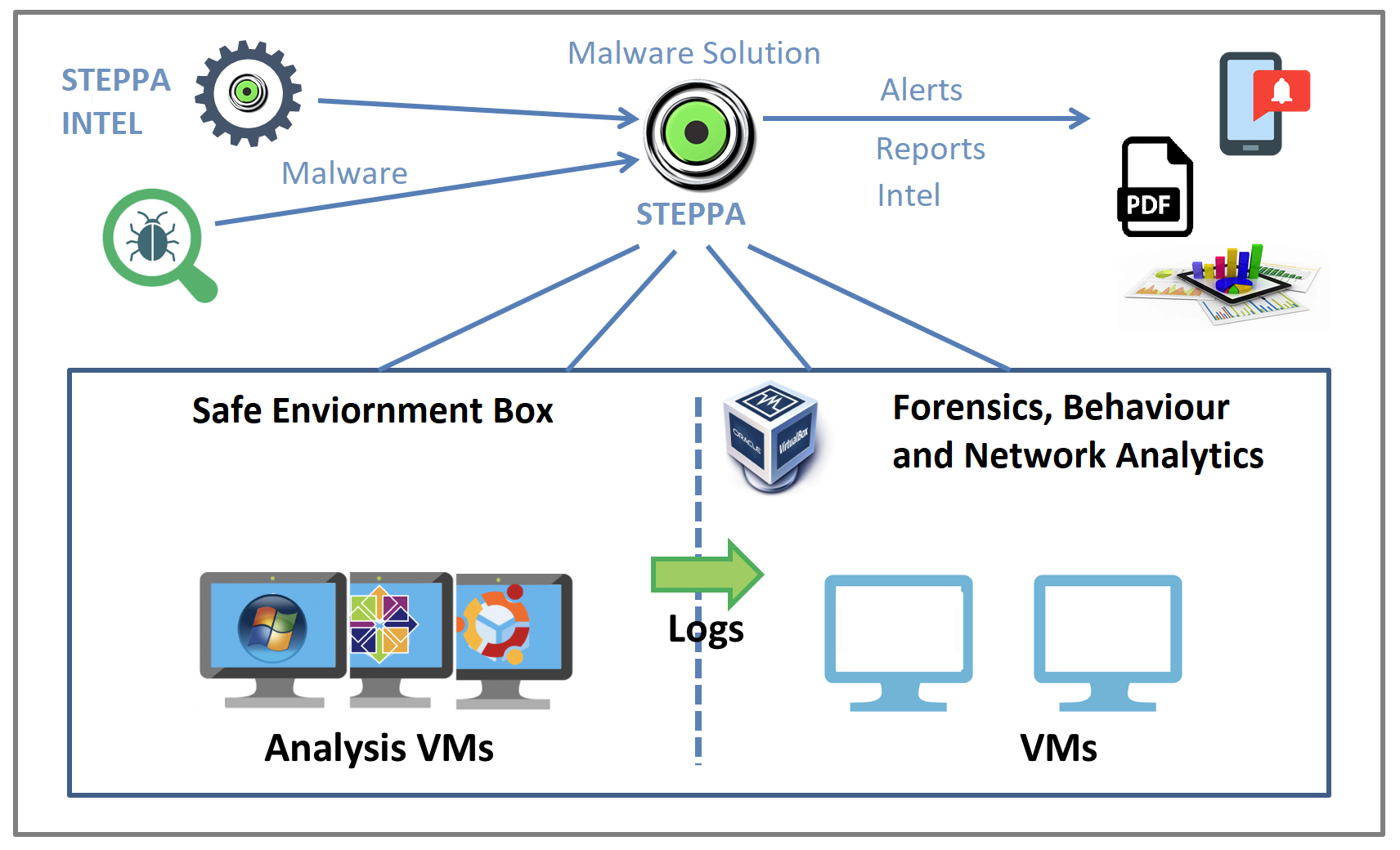
Malware Analysis Solution: Analyze, Detect, and Protect

FBI, CISA, MS-ISAC release cybersecurity advisory on emerging Rhysida ransomware targeting critical sectors - Industrial Cyber

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog

Info stealers and how to protect against them

MetaDefender Cloud Advanced threat prevention and detection

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen

Malware analysis AIO_4.9.8__ed.rar Malicious activity

Malware analysis index.html Malicious activity

Malware Analysis: Steps & Examples - CrowdStrike

Malware Analysis: Steps & Examples - CrowdStrike

Detail procedure of malware analysis
Recomendado para você
-
 FUT1 ARENA MAX Futebol ao vivo para Android - Download03 março 2025
FUT1 ARENA MAX Futebol ao vivo para Android - Download03 março 2025 -
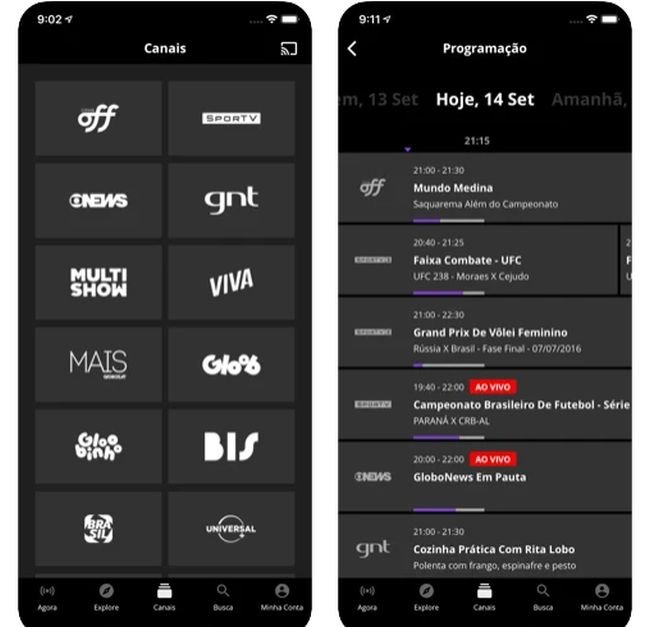 8 melhores aplicativos para assistir futebol - TecMundo03 março 2025
8 melhores aplicativos para assistir futebol - TecMundo03 março 2025 -
 Toon Cup, Football Games03 março 2025
Toon Cup, Football Games03 março 2025 -
 Bola De Futebol No Pictograma Líquido PNG , Internet, Rede De Futebol, Gol Imagem PNG e Vetor Para Download Gratuito03 março 2025
Bola De Futebol No Pictograma Líquido PNG , Internet, Rede De Futebol, Gol Imagem PNG e Vetor Para Download Gratuito03 março 2025 -
 Free Google Slides & PowerPoint templates about Football03 março 2025
Free Google Slides & PowerPoint templates about Football03 março 2025 -
S.O.S Canais03 março 2025
-
 Futebol, Sociedade E Política :: Comofazerumtccdeeducaofisicalicenciatura03 março 2025
Futebol, Sociedade E Política :: Comofazerumtccdeeducaofisicalicenciatura03 março 2025 -
 Soccer Flyer Images - Free Download on Freepik03 março 2025
Soccer Flyer Images - Free Download on Freepik03 março 2025 -
AuriSat Catunda CE03 março 2025
-
 Futebol ao vivo na TV: confira os melhores apps para assistir jogos03 março 2025
Futebol ao vivo na TV: confira os melhores apps para assistir jogos03 março 2025
você pode gostar
-
 Eu joguei Stumble Guys pela primeira vez e…03 março 2025
Eu joguei Stumble Guys pela primeira vez e…03 março 2025 -
Mod Structures for Minecraft – Apps no Google Play03 março 2025
-
 Create Animated GIFs with Mac OS X Preview.app – Robert Harder, PhD03 março 2025
Create Animated GIFs with Mac OS X Preview.app – Robert Harder, PhD03 março 2025 -
 Entenda quem é Adam e Eve em NieR: Automata Ver1.1a - Critical Hits03 março 2025
Entenda quem é Adam e Eve em NieR: Automata Ver1.1a - Critical Hits03 março 2025 -
What do you use Typeform for? - Quora03 março 2025
-
 Primeira a funcionar 24h na capital, Drogaria São Paulo completa03 março 2025
Primeira a funcionar 24h na capital, Drogaria São Paulo completa03 março 2025 -
 Summer Time Rendering, 4K, anime, Anime screenshot, anime boys, anime girls03 março 2025
Summer Time Rendering, 4K, anime, Anime screenshot, anime boys, anime girls03 março 2025 -
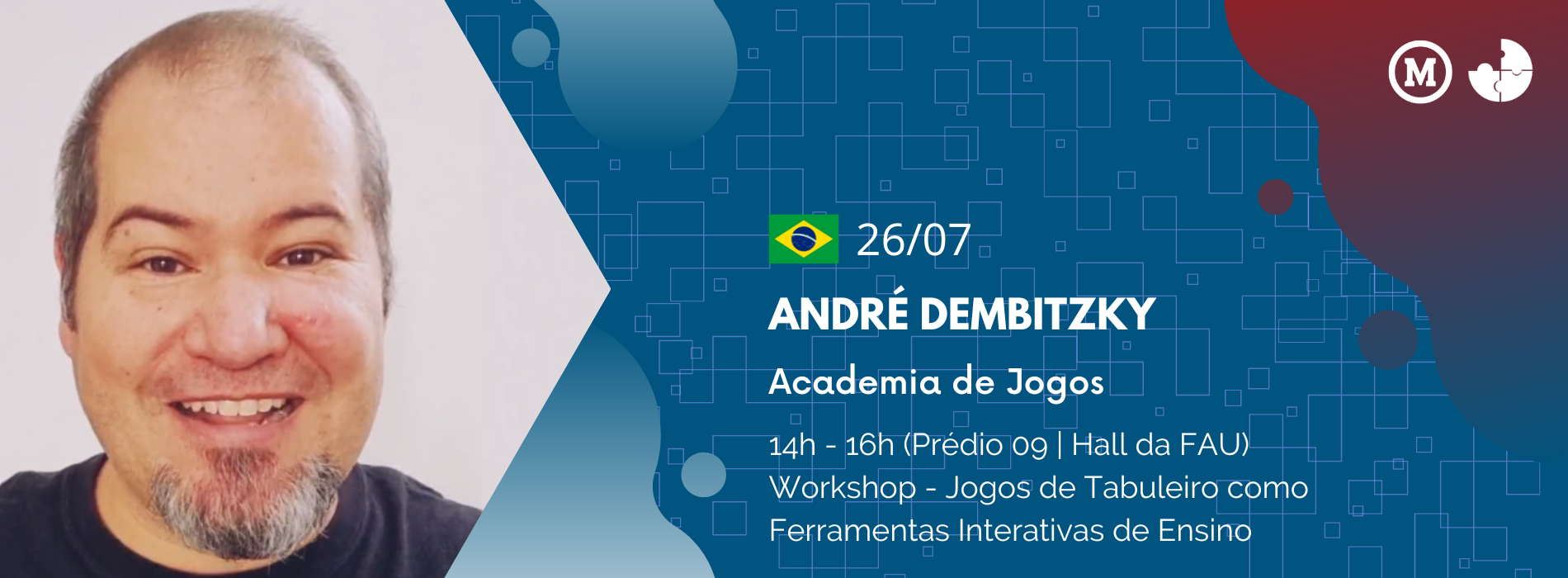 VII FÓRUM Aprendizagem Transformadora03 março 2025
VII FÓRUM Aprendizagem Transformadora03 março 2025 -
 Velma Season 1 Trailer03 março 2025
Velma Season 1 Trailer03 março 2025 -
Ajin Episode 5 Discussion - Forums03 março 2025


