Malware analysis Malicious activity
Por um escritor misterioso
Last updated 18 fevereiro 2025
Malware analysis Malicious activity

Routers Roasting on an Open Firewall: the KV-botnet Investigation - Lumen
Interactive Online Malware Sandbox

Info stealers and how to protect against them

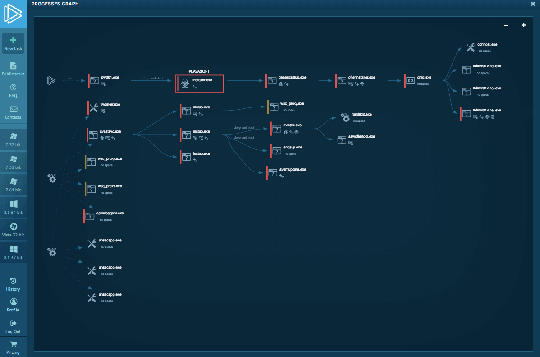
Malware analysis metasploit.bat Malicious activity
Lab 6-1 Solutions - Practical Malware Analysis [Book]

How to Analyze Malware's Network Traffic in A Sandbox

Advanced Automated Malware Analysis – Kaspersky Research Sandbox

Playbook of the Week: Malware Investigation and Response - Palo Alto Networks Blog

Patch Now: Exploit Activity Mounts for Dangerous Apache Struts 2 Bug

Endpoint Detection and Response, Free - What is EDR Security?

Malware analysis index.html Malicious activity
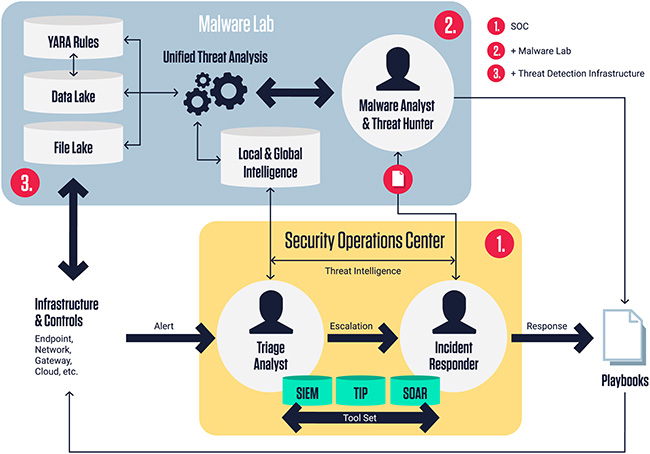
ReversingLabs Malware Lab: Detect, classify, analyze, and respond to malicious files - Help Net Security
Recomendado para você
-
 Bubbles Shooter - Free Play & No Download18 fevereiro 2025
Bubbles Shooter - Free Play & No Download18 fevereiro 2025 -
 Bubble Time Blast Shooter - New Funny Games by Wichuda Maneekham18 fevereiro 2025
Bubble Time Blast Shooter - New Funny Games by Wichuda Maneekham18 fevereiro 2025 -
 Bouncing Balls - Play Online on SilverGames 🕹️18 fevereiro 2025
Bouncing Balls - Play Online on SilverGames 🕹️18 fevereiro 2025 -
 Pin on Acessórios iphone18 fevereiro 2025
Pin on Acessórios iphone18 fevereiro 2025 -
 Bubble Shooter Birds. Lets play. Funny game.18 fevereiro 2025
Bubble Shooter Birds. Lets play. Funny game.18 fevereiro 2025 -
 Ramon van der Burgt - Graphic Designer18 fevereiro 2025
Ramon van der Burgt - Graphic Designer18 fevereiro 2025 -
 Premium Vector Children active games infographic with funny games round dances hopscotch board and catch up games descriptions vector illustration18 fevereiro 2025
Premium Vector Children active games infographic with funny games round dances hopscotch board and catch up games descriptions vector illustration18 fevereiro 2025 -
 Bubble Time Blast Shooter - New Funny Games18 fevereiro 2025
Bubble Time Blast Shooter - New Funny Games18 fevereiro 2025 -
 Bubble Shooter 318 fevereiro 2025
Bubble Shooter 318 fevereiro 2025 -
 Italian games for children to play outside (Part 2) - Sos Italian18 fevereiro 2025
Italian games for children to play outside (Part 2) - Sos Italian18 fevereiro 2025
você pode gostar
-
 Lords of the Fallen Collector's Edition Xbox Series X 🔥 PRE ORDER18 fevereiro 2025
Lords of the Fallen Collector's Edition Xbox Series X 🔥 PRE ORDER18 fevereiro 2025 -
 Gatos Guerreiros Quiz (Quem sou eu?)18 fevereiro 2025
Gatos Guerreiros Quiz (Quem sou eu?)18 fevereiro 2025 -
 Mommy Long Legs (Poppy Playtime: Chapter 2) - Coffin Dance Song18 fevereiro 2025
Mommy Long Legs (Poppy Playtime: Chapter 2) - Coffin Dance Song18 fevereiro 2025 -
 Brinquedo Roblox Brookhaven St. Luke's Hospital c/ código18 fevereiro 2025
Brinquedo Roblox Brookhaven St. Luke's Hospital c/ código18 fevereiro 2025 -
 Troll Face png download - 1280*924 - Free Transparent Goblin png Download. - CleanPNG / KissPNG18 fevereiro 2025
Troll Face png download - 1280*924 - Free Transparent Goblin png Download. - CleanPNG / KissPNG18 fevereiro 2025 -
Blox Fruits Values - Permanent Mythical Fruits18 fevereiro 2025
-
 Qual a ordem certa para ver Monogatari Series?18 fevereiro 2025
Qual a ordem certa para ver Monogatari Series?18 fevereiro 2025 -
Meme Fandom18 fevereiro 2025
-
Local Games18 fevereiro 2025
-
JUST IN: Chainsaw Man has release the - Anime Corner News18 fevereiro 2025



