Indirect Command Execution – Penetration Testing Lab
Por um escritor misterioso
Last updated 21 fevereiro 2025

The windows ecosystem provides multiple binaries that could be used by adversaries to execute arbitrary commands that will evade detection especially in environments that are monitoring binaries such as "cmd.exe". In certain occasions the techniques described below could be used to bypass application whitelisting products if rules are not configured properly (whitelist by path or…
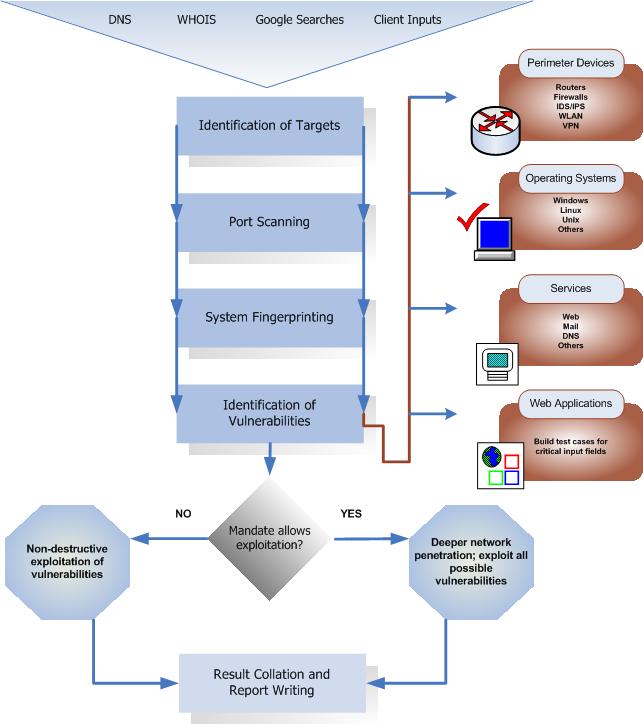
Penetration Testing Execution Standard

Indirect Command Execution – Penetration Testing Lab

Indirect Command Execution: Defense Evasion (T1202) - Hacking Articles
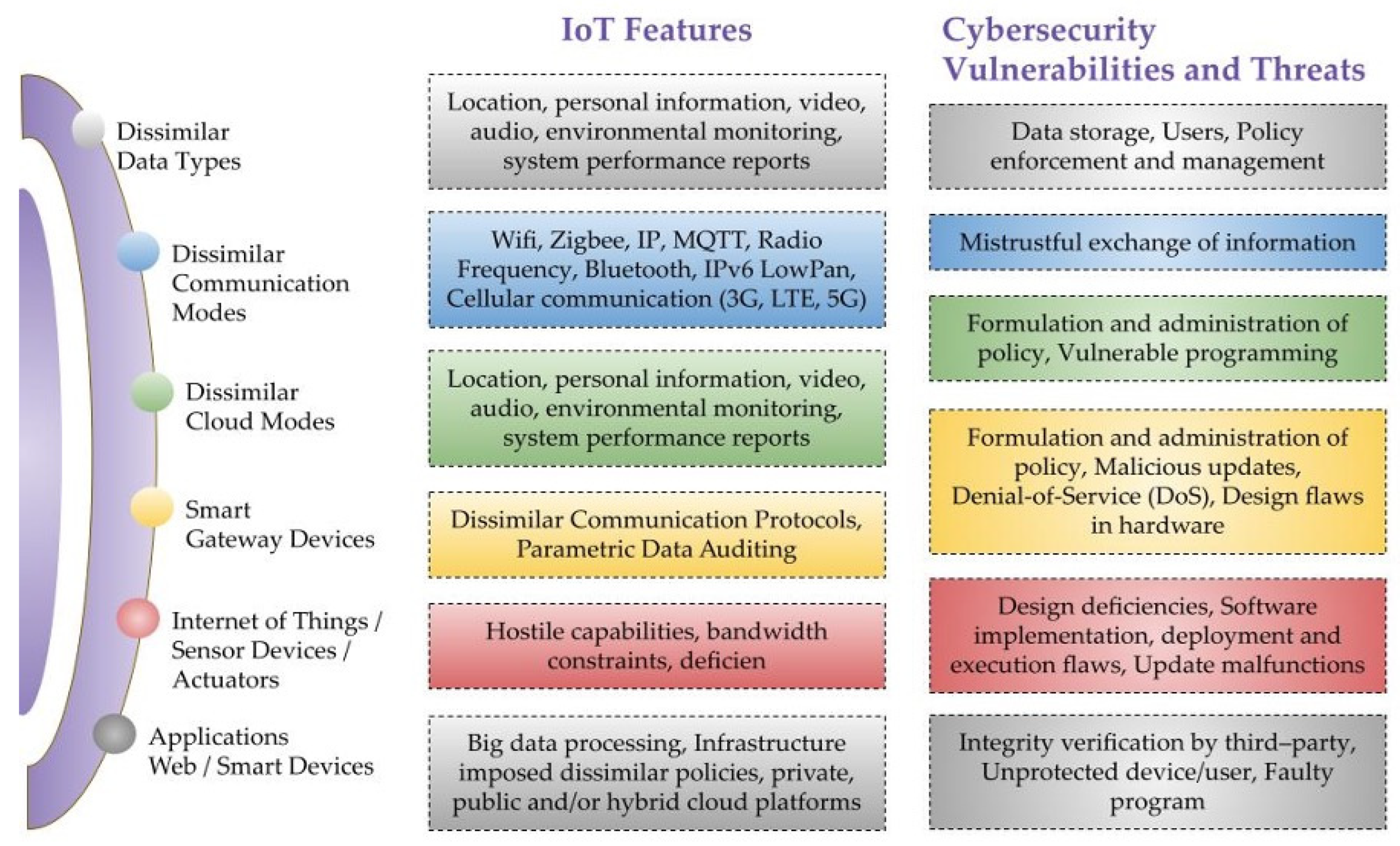
Sensors, Free Full-Text

How prepared is the world? Identifying weaknesses in existing assessment frameworks for global health security through a One Health approach - The Lancet

Security Testing: Types, Tools, and Best Practices

Blind SQL Injection: An Expert's Guide to Detect and Exploit
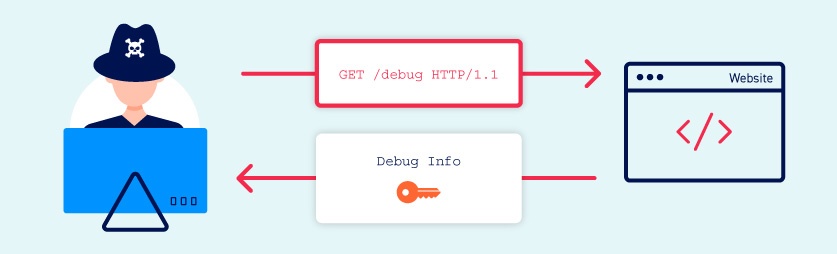
Information disclosure vulnerabilities

TryHackMe Hacktivities

Art of Software Security Testing, The: Identifying Software Security Flaws: Identifying Software Security Flaws: Wysopal, Chris: 0884181946483: : Books

File Inclusion Vulnerabilities: What are they and how do they work?

Kali Linux Web Penetration Testing Cookbook
Recomendado para você
-
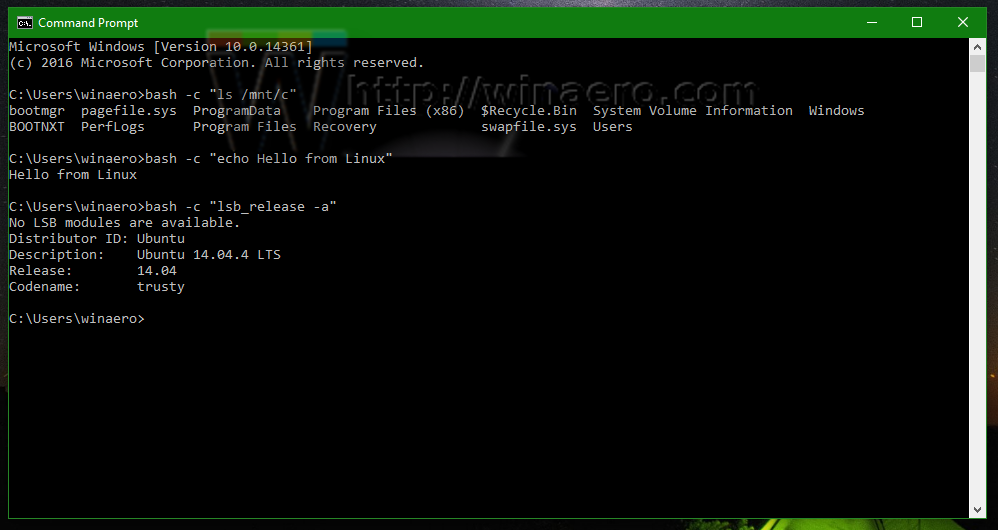 Run Linux commands from cmd.exe prompt in Windows 1021 fevereiro 2025
Run Linux commands from cmd.exe prompt in Windows 1021 fevereiro 2025 -
 How to Run an EXE File at the Command Prompt in 8 Easy Steps21 fevereiro 2025
How to Run an EXE File at the Command Prompt in 8 Easy Steps21 fevereiro 2025 -
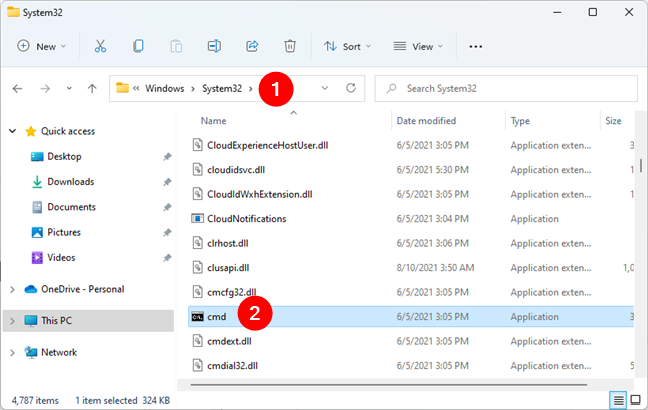 How to open Command Prompt (14 ways) - Digital Citizen21 fevereiro 2025
How to open Command Prompt (14 ways) - Digital Citizen21 fevereiro 2025 -
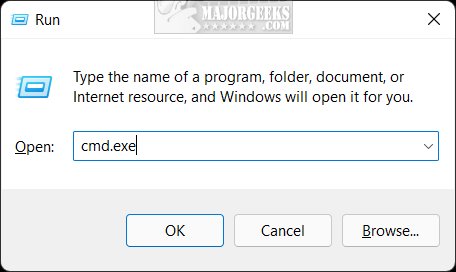 10 Ways to Open the Command Prompt in Windows 11 - MajorGeeks21 fevereiro 2025
10 Ways to Open the Command Prompt in Windows 11 - MajorGeeks21 fevereiro 2025 -
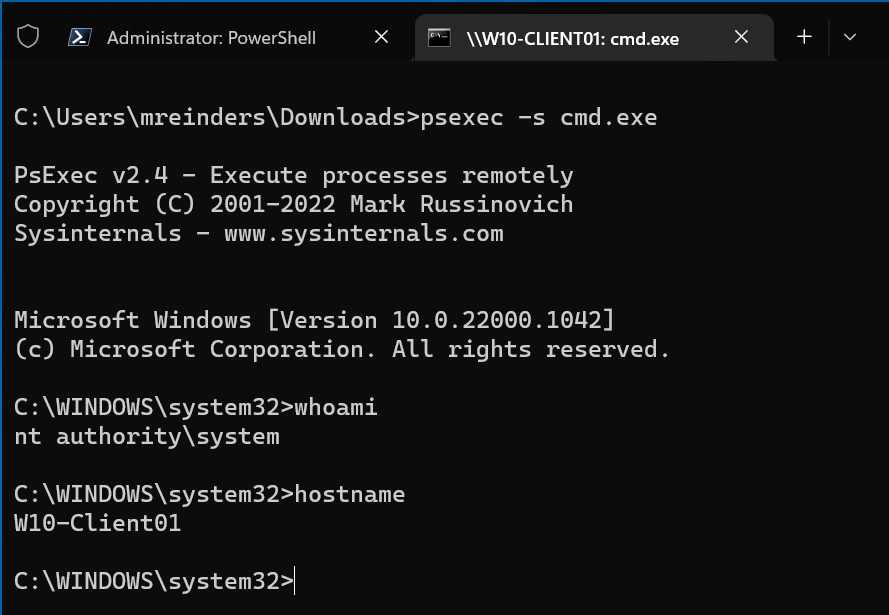 How to Run Commands and Programs Remotely Using PsExec21 fevereiro 2025
How to Run Commands and Programs Remotely Using PsExec21 fevereiro 2025 -
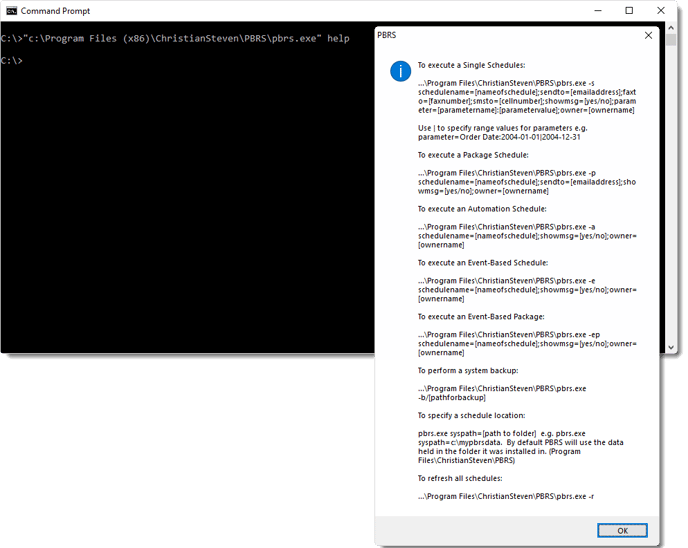 How do I use Command Line Options in PBRS?21 fevereiro 2025
How do I use Command Line Options in PBRS?21 fevereiro 2025 -
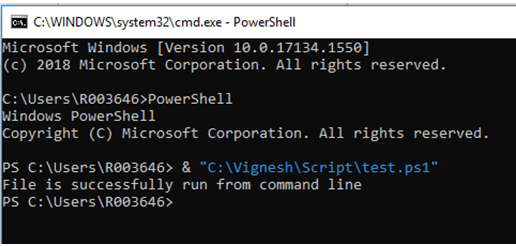 Start PowerShell from cmd Examples of Start PowerShell from cmd21 fevereiro 2025
Start PowerShell from cmd Examples of Start PowerShell from cmd21 fevereiro 2025 -
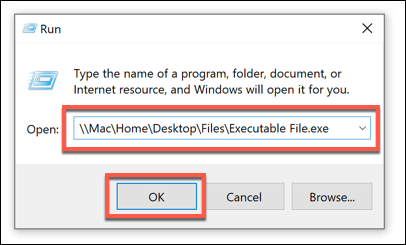 What Is An Executable File & How To Create One21 fevereiro 2025
What Is An Executable File & How To Create One21 fevereiro 2025 -
![wine - How to run dos [ent.exe] and [fp8.exe] on Ubuntu? - Ask Ubuntu](https://i.stack.imgur.com/DHchp.png) wine - How to run dos [ent.exe] and [fp8.exe] on Ubuntu? - Ask Ubuntu21 fevereiro 2025
wine - How to run dos [ent.exe] and [fp8.exe] on Ubuntu? - Ask Ubuntu21 fevereiro 2025 -
 asp.net - How to run cmd.exe using c# with multiple arguments? - Stack Overflow21 fevereiro 2025
asp.net - How to run cmd.exe using c# with multiple arguments? - Stack Overflow21 fevereiro 2025
você pode gostar
-
 Pokémon Reshiram GX SV51/SV94 Hidden Fates Shiny Metal Gold Card Rare for Sale in Brooklyn, NY - OfferUp21 fevereiro 2025
Pokémon Reshiram GX SV51/SV94 Hidden Fates Shiny Metal Gold Card Rare for Sale in Brooklyn, NY - OfferUp21 fevereiro 2025 -
 Duelo do Inglês tem empate e comemoração antissemita de Anelka21 fevereiro 2025
Duelo do Inglês tem empate e comemoração antissemita de Anelka21 fevereiro 2025 -
 HM02 FLY - Pokemon Fire Red / Leaf Green21 fevereiro 2025
HM02 FLY - Pokemon Fire Red / Leaf Green21 fevereiro 2025 -
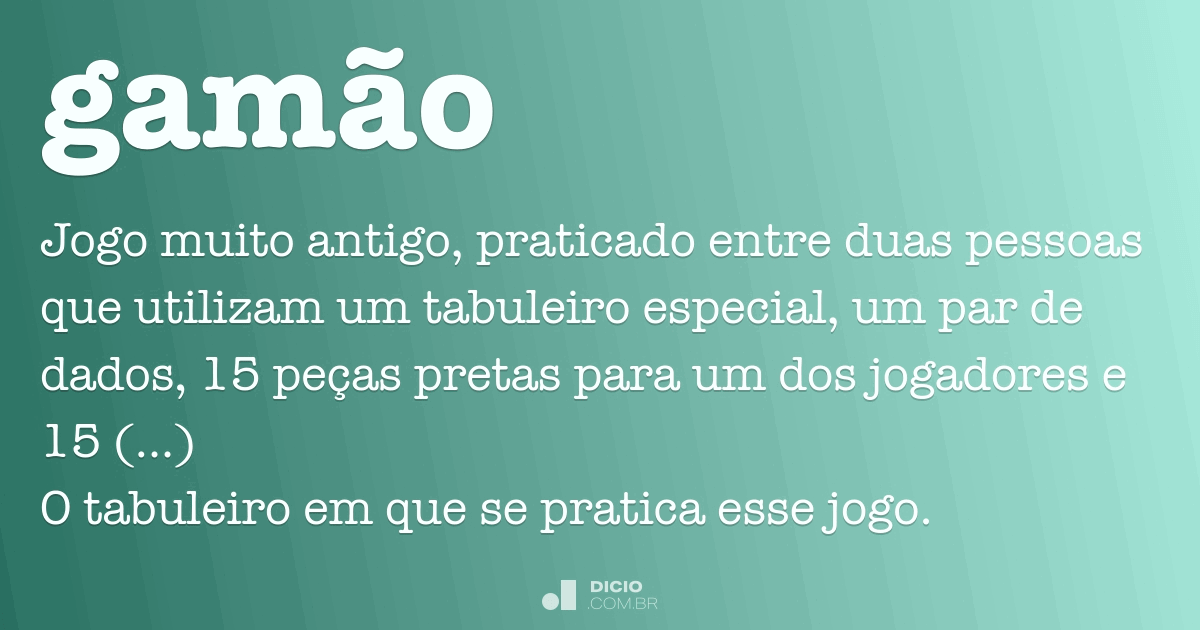 Gamão - Dicio, Dicionário Online de Português21 fevereiro 2025
Gamão - Dicio, Dicionário Online de Português21 fevereiro 2025 -
 Papi Drive APK for Android - Download21 fevereiro 2025
Papi Drive APK for Android - Download21 fevereiro 2025 -
 Quantum Leap' Sequel Series Pilot at NBC Rounds Out Main Cast21 fevereiro 2025
Quantum Leap' Sequel Series Pilot at NBC Rounds Out Main Cast21 fevereiro 2025 -
 Red Dead Wiki Red Dead+BreezeWiki21 fevereiro 2025
Red Dead Wiki Red Dead+BreezeWiki21 fevereiro 2025 -
 Mairimashita IRUMA KUN Anime pra dar HAHAHAs e KKKKs - Análise21 fevereiro 2025
Mairimashita IRUMA KUN Anime pra dar HAHAHAs e KKKKs - Análise21 fevereiro 2025 -
플리캠 4K 가로] Billlie TSUKI 'GingaMingaYo(the strange world)'(빌리 츠키 직캠) l Simply K-Pop CON-TOUR Ep.508 - allkpop forums21 fevereiro 2025
-
 Rogues Rising Update Notes - Rogue Company Wiki21 fevereiro 2025
Rogues Rising Update Notes - Rogue Company Wiki21 fevereiro 2025