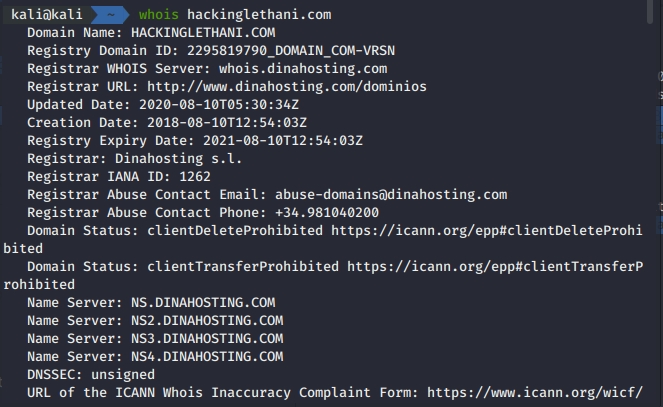
Infrastructure Hacking: WHOIS Protocol » Hacking Lethani
Por um escritor misterioso
Last updated 19 dezembro 2024
Did you know that the Secure Shell protocol, better known as SSH, is not as secure as its name suggests? In this post I show you different ways to attack this protocol. %

Learn ethical hacking (@learn_hacking4) • Instagram photos and videos

tl;dr sec] #169 - Top 10 Web Hacking Techniques of 2022, Finding Malicious Dependencies, Fearless CORS
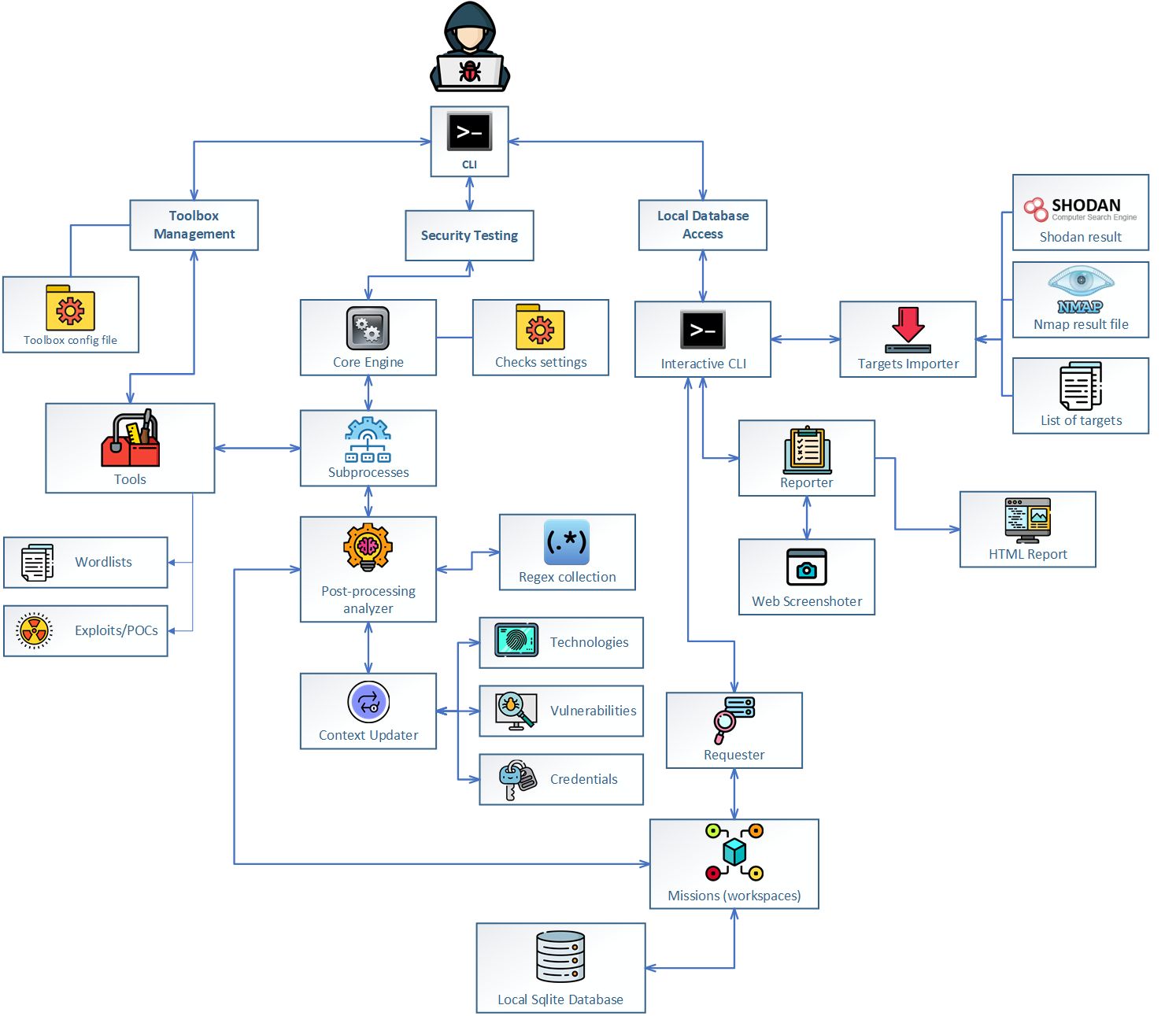
Jok3r v3 BETA 2 - Network and Web Pentest Automation Framework

Your IT Provider Is Letting Hackers Into Your Business”
Ronin Hack: North Korea's Lazarus Behind $540 Million Axe Infinity Breach

Infrastructure Hacking: WHOIS Protocol » Hacking Lethani

7 powerful pentesting tools (& why you should stop pedestalizing them)

Hacking Tutorial - Ethical Hacking Tutorial - Wikitechy

Infrastructure Hacking: WHOIS Protocol » Hacking Lethani

tl;dr sec] #169 - Top 10 Web Hacking Techniques of 2022, Finding Malicious Dependencies, Fearless CORS
Recomendado para você
-
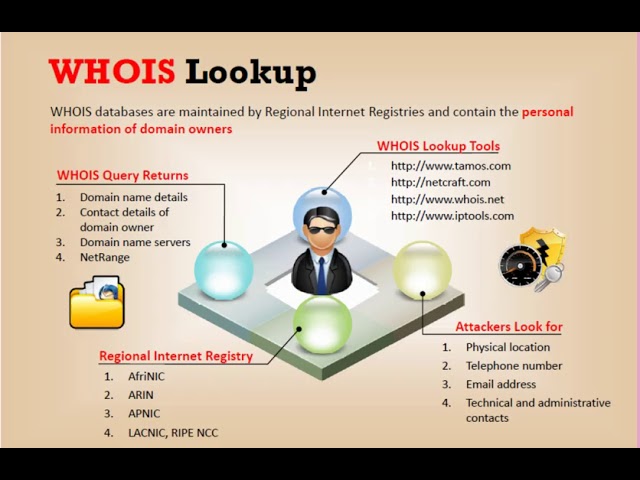 What is the WHOIS lookup19 dezembro 2024
What is the WHOIS lookup19 dezembro 2024 -
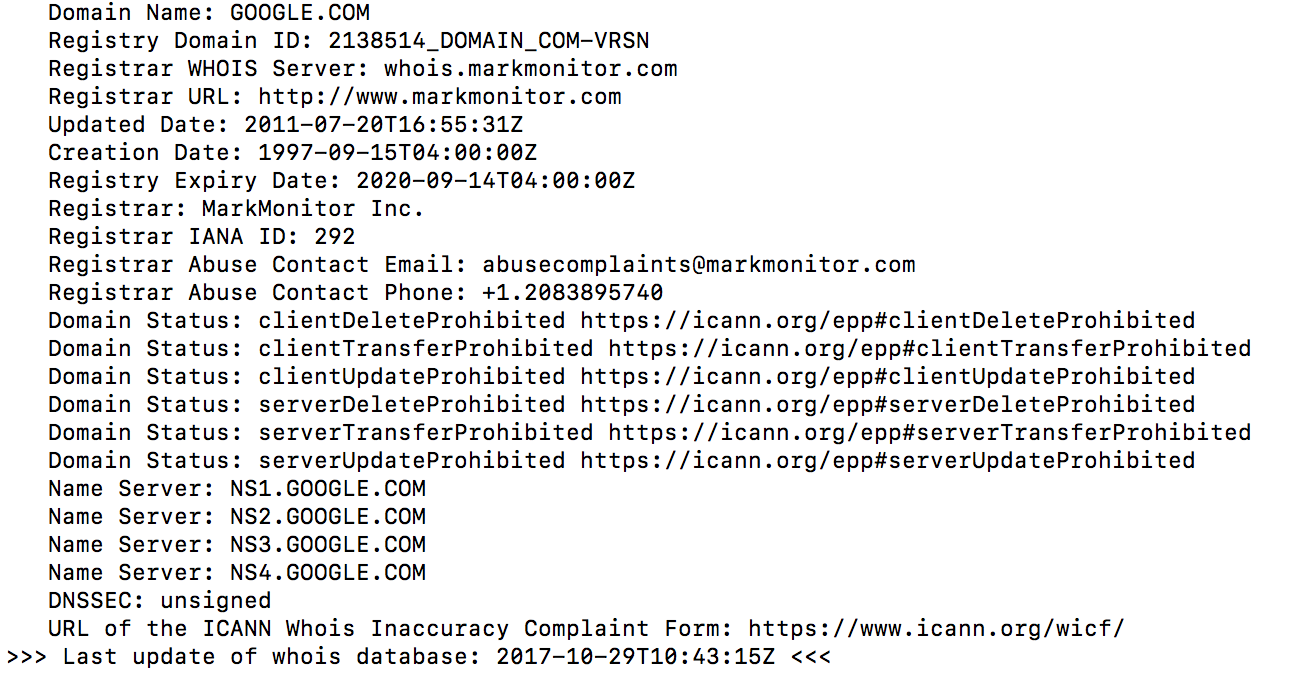 All you need to know about Linux whois command (domain lookup19 dezembro 2024
All you need to know about Linux whois command (domain lookup19 dezembro 2024 -
 WHOIS Domain Lookup - Find out who owns a website - GoDaddy19 dezembro 2024
WHOIS Domain Lookup - Find out who owns a website - GoDaddy19 dezembro 2024 -
 What is WHOIS and How Does it Work? (+ Tips on Free Domain Privacy)19 dezembro 2024
What is WHOIS and How Does it Work? (+ Tips on Free Domain Privacy)19 dezembro 2024 -
Whois powers global expansion with OCI's scalability and performance19 dezembro 2024
-
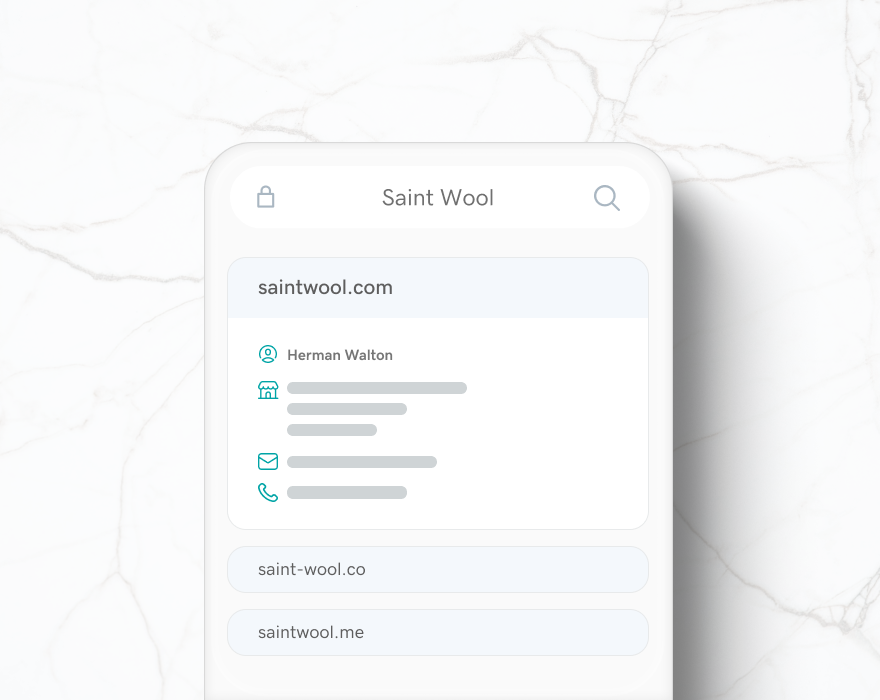
 Whois Lookup: How to Check Domain Availability & Expiry Date19 dezembro 2024
Whois Lookup: How to Check Domain Availability & Expiry Date19 dezembro 2024 -
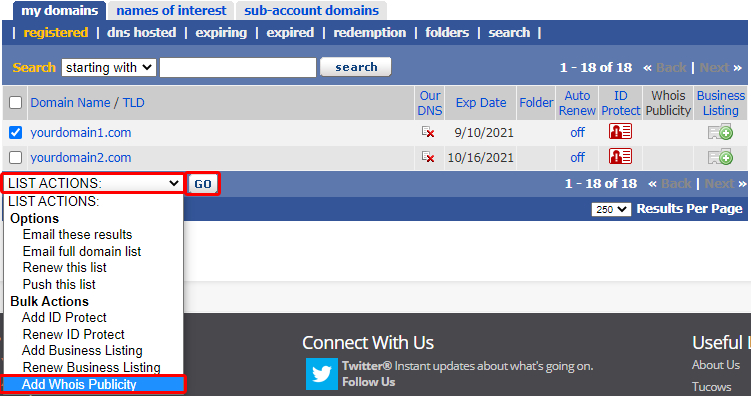 Whois Publicity – Help & Support19 dezembro 2024
Whois Publicity – Help & Support19 dezembro 2024 -
 Whois - Download19 dezembro 2024
Whois - Download19 dezembro 2024 -
Whois Icon19 dezembro 2024
-
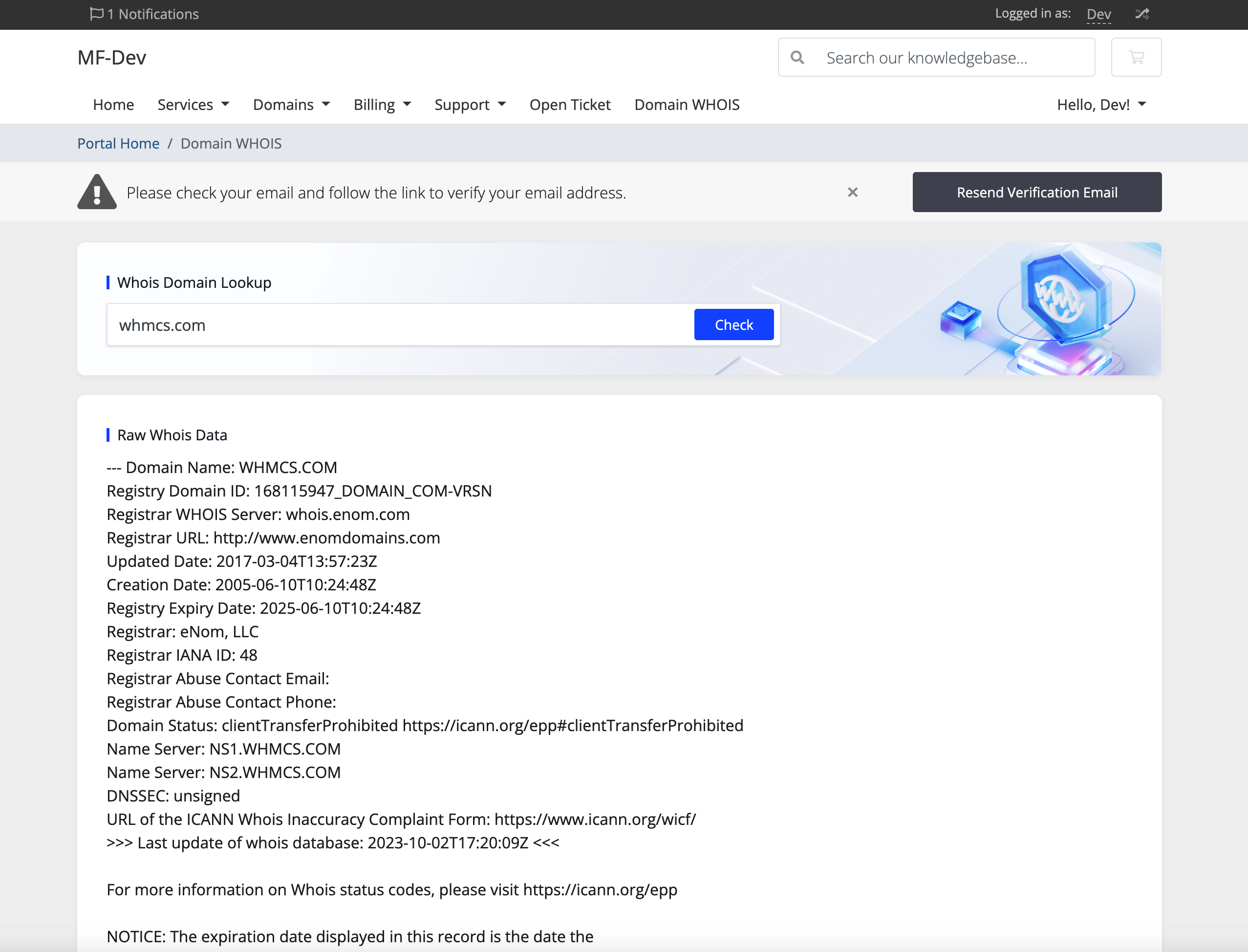 Domain WHOIS Checker - WHMCS Marketplace19 dezembro 2024
Domain WHOIS Checker - WHMCS Marketplace19 dezembro 2024
você pode gostar
-
 Call of Duty: Modern Warfare III Campaign: How to Play — news19 dezembro 2024
Call of Duty: Modern Warfare III Campaign: How to Play — news19 dezembro 2024 -
 Tofu Salad - Marcoca19 dezembro 2024
Tofu Salad - Marcoca19 dezembro 2024 -
 Shiden Ritter (Suoh City) - Scarlet Nexus Guide - IGN19 dezembro 2024
Shiden Ritter (Suoh City) - Scarlet Nexus Guide - IGN19 dezembro 2024 -
 Novo acordo ortográfico: o que mudou, exemplos - Brasil Escola19 dezembro 2024
Novo acordo ortográfico: o que mudou, exemplos - Brasil Escola19 dezembro 2024 -
 Rhythm Tengoku Gold- DS Game- New Japan Import : Video Games19 dezembro 2024
Rhythm Tengoku Gold- DS Game- New Japan Import : Video Games19 dezembro 2024 -
 Xadrez chinês imagem de stock. Imagem de social, chinês - 20922942919 dezembro 2024
Xadrez chinês imagem de stock. Imagem de social, chinês - 20922942919 dezembro 2024 -
 Pin de Shirley Faustino em 1 EM Planos de estudo enem, Notação19 dezembro 2024
Pin de Shirley Faustino em 1 EM Planos de estudo enem, Notação19 dezembro 2024 -
 Bancários CGR - Área de Lazer19 dezembro 2024
Bancários CGR - Área de Lazer19 dezembro 2024 -
 Protestos no Irã se encaminham para o terceiro mês – Monitor do Oriente19 dezembro 2024
Protestos no Irã se encaminham para o terceiro mês – Monitor do Oriente19 dezembro 2024 -
![Justin Bieber - One time [Tradução/Legendado]](https://i.ytimg.com/vi/XbFigKlw-ao/maxresdefault.jpg) Justin Bieber - One time [Tradução/Legendado]19 dezembro 2024
Justin Bieber - One time [Tradução/Legendado]19 dezembro 2024